Did you know that 50% of UK businesses experienced a cyber attack in the last 12 months? You’ve likely felt the pressure of keeping your data safe while balancing the books, and it’s frustrating when reactive cyber security services lead to hidden costs rather than true protection. We understand that North East business owners want to focus on growth, not lose sleep over the latest NIS2 compliance update or the threat of a business-ending breach.
Our award-winning team is here to show you how proactive cyber security services protect your operations and simplify complex regulations. You’ll discover how to build a secure, “always-on” environment that provides the long-term peace of mind your business deserves. This guide breaks down the clear ROI of modern security and explains why a trusted North East partner is your best defense. Let’s look at how you can move from reactive stress to a resilient, expert-led strategy for 2026 and beyond.
Key Takeaways
- Learn how proactive cyber security services move your business beyond the costly “break-fix” trap to ensure continuous uptime and operational resilience.
- Discover why modern “Zero Trust” architectures and layered defenses are essential for protecting your critical data against 2026’s sophisticated digital threats.
- Follow our 5-step framework to conduct a comprehensive security audit and identify potential entry points before they can be exploited.
- Understand the value of partnering with an award-winning team that combines technical authority with a local, North East approach to your business security.
What are Cyber Security Services? Defining Resilience in 2026
Cyber security services represent a holistic set of proactive technologies and protocols designed to protect your digital assets before a breach occurs. In 2026, the old method of building a high wall around your office network is obsolete. Modern protection relies on “Zero Trust” architectures where every user and device must be continuously verified, regardless of their location. This shift prioritises business continuity over simple threat detection, ensuring your operations stay live even during an attempted exploit. For a foundational look at the field, Wikipedia’s overview of computer security provides an excellent breakdown of the core principles involved. Cyber Resilience is the ability to anticipate, withstand, and recover from attacks.
The Evolution of Managed Security
Traditional antivirus software can’t keep pace with the AI-driven threats we see today. Hackers now use automated tools to launch sophisticated, polymorphic attacks that bypass standard signatures. Our award-winning approach replaces passive software with 24/7 monitoring through a dedicated Security Operations Centre (SOC). This ensures that experts are watching your network every second of the day. Managed services create a seamless layer of protection for your remote and hybrid teams, securing home Wi-Fi and mobile devices as tightly as your main office. It’s about proactive intervention, not just reactive clean-up.
Why Proactive Security is a Business Enabler
Our North East based team understands that you need more than just a tech fix. You need a partner who ensures your business stays resilient. We simplify the complex world of cyber security services so you can focus on what you do best: growing your company.
- Proactive threat hunting to stop attacks before they land.
- Zero Trust frameworks to secure your hybrid workforce.
- Continuous monitoring to provide 24/7 peace of mind.
Proactive vs. Reactive Security: Choosing the Right Approach
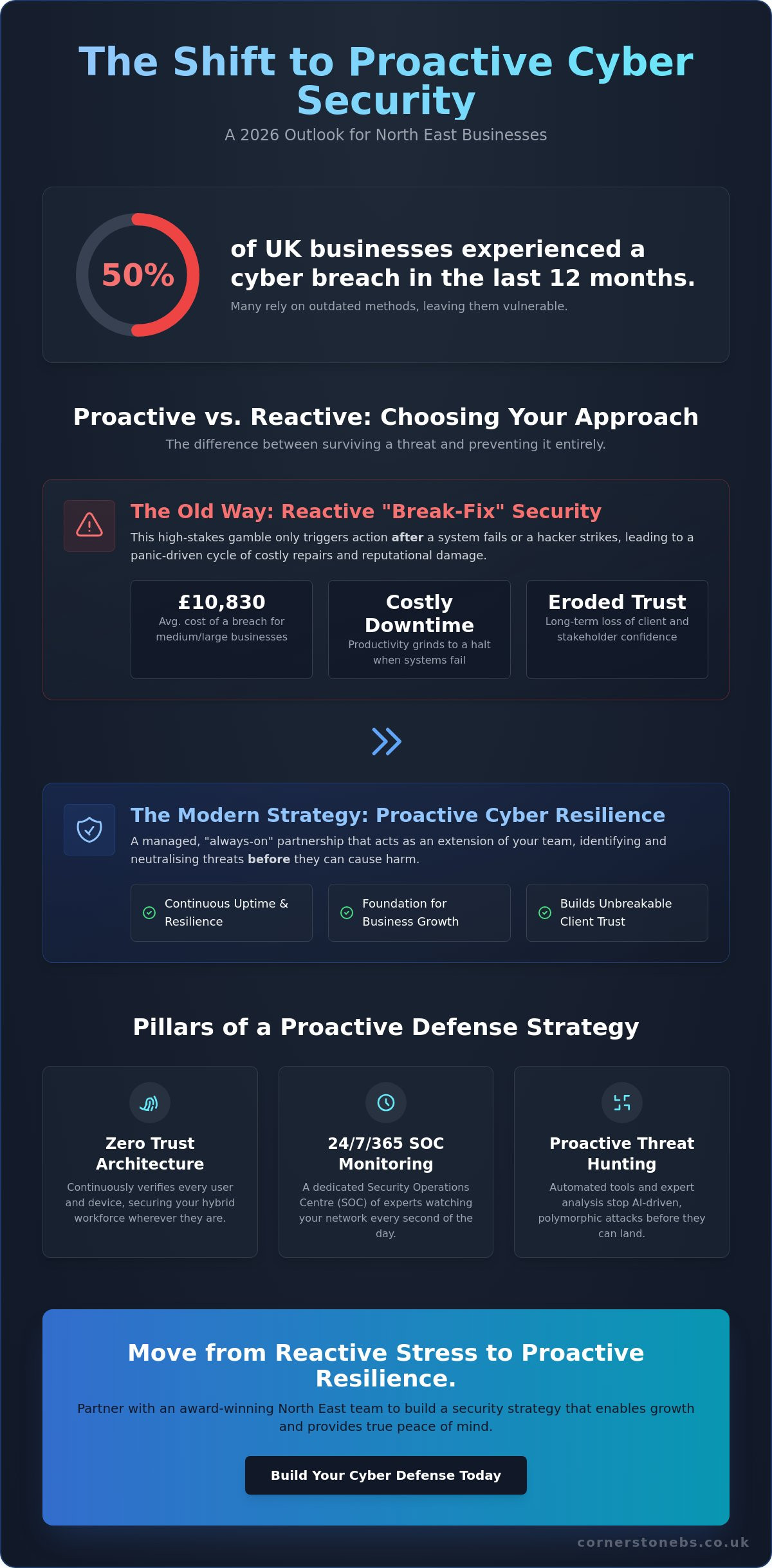
Many businesses still rely on the outdated “break-fix” model. This approach only triggers action after a system fails or a hacker strikes. It is a high-stakes gamble that often ends in costly downtime. Our award-winning cyber security services move your business away from this panic-driven cycle. Instead, we implement a managed proactive support system. We act as a seamless extension of your internal team, watching your network while you focus on growth. This partnership model ensures that potential threats are neutralised before they ever reach your front door.
Reactive security carries hidden burdens that go beyond a simple repair bill. When systems go dark, productivity stops. A 2024 UK government report found that the average cost of a cyber breach for medium and large businesses reached £10,830. For many North East SMEs, that is a hit that impacts the bottom line for years. Proactive monitoring identifies vulnerabilities, such as unpatched software or weak credentials, before attackers exploit them. It is the difference between installing a fire alarm and having a 24/7 fire marshal on site.
The Real Cost of a Data Breach
Financial losses are just the start. The long-term erosion of customer confidence is often much harder to repair. If a client’s data is compromised, they won’t remember how fast you fixed the server; they will remember that their trust was broken. Our proactive audits and ransomware protection for UK businesses are designed to stop these scenarios in their tracks. By identifying risks early, we protect your reputation as much as your data. If you’re unsure about your current setup, we’re always happy to have a quick chat about your needs.
Achieving Peace of Mind Through Automation
Modern cloud environments move too fast for manual checks. We use automated patch management to ensure every system update is applied the moment it is released. This automation significantly reduces the “Mean Time to Detect” (MTTD) an incident. A robust cyber resilience strategy relies on these always-on systems to provide 24/7 protection. Our local experts use these tools to provide real-time alerts, giving you the confidence that your business is secure even when your office lights are off. This level of automation is no longer a luxury; it is a foundational requirement for any business operating in 2026.
The Four Pillars of Robust Cyber Security Services
Building a resilient business in 2026 requires more than just a single piece of software. We view effective cyber security services as a layered defense strategy, often called Defense in Depth. This approach ensures that if one barrier fails, others are ready to catch the threat. It’s vital to remember that no single tool is a silver bullet for security; true protection comes from how these layers interact. By referencing resources like the CISA Services Catalog, our award-winning team helps you understand the breadth of protection required to keep your operations running smoothly. We focus on creating a “robust” environment where every digital door is locked and monitored.
Protecting Your People: The Human Firewall
Your employees are your first and last line of defense. Ongoing security awareness training transforms them into a “human firewall” capable of spotting sophisticated social engineering. Multi-Factor Authentication (MFA) remains a non-negotiable standard for any modern firm. Industry data from Microsoft suggests that MFA prevents 99.9% of bulk password attacks, making it one of the most effective tools in your arsenal. We also implement regular phishing simulations. These exercises build a security-first culture where staff feel confident identifying risks rather than falling victim to them. It turns a potential weakness into a proactive strength.
Securing the Network and Cloud Environment
The traditional office perimeter has evolved. Our approach combines next-generation firewalls with encrypted VPNs to create a secure tunnel for your data. As more North East firms adopt cloud solutions, we integrate security directly into the infrastructure. This allows for secure scaling without exposing your assets. Endpoint protection is equally critical. It secures every laptop, tablet, and smartphone used by your team, whether they’re working in Teesside or from a home office. This ensures your network remains airtight regardless of where your staff log in.
Governance, Risk, and Compliance (GRC)
Compliance is about more than just avoiding fines; it’s about establishing trust with your partners. Navigating the complexities of NIS2 and UK GDPR can feel overwhelming for a busy business owner. We simplify this by aligning your systems with the Cyber Essentials and Cyber Essentials Plus frameworks. These UK-backed certifications act as a badge of quality for your clients. Regular vulnerability scanning is a core part of this pillar. It helps us proactively identify and patch weaknesses before they can be exploited. This structured approach to cyber security services provides you with the long-term peace of mind you need to focus on growth.
Building Your Cyber Resilience Strategy: A 5-Step Framework
Resilience isn’t just about stopping attacks; it’s about how quickly your business bounces back. In 2026, the complexity of threats requires a structured, proactive approach. Our award-winning team uses a proven 5-step framework to ensure your cyber security services provide a solid foundation for growth.
- Audit: We start with a comprehensive infrastructure assessment. According to the UK Government’s Cyber Security Breaches Survey 2024, 50% of UK businesses identified a breach or attack in the previous 12 months. An audit identifies these vulnerabilities before they’re exploited.
- Identify: You can’t protect what you don’t know you have. We map out your critical data assets and every potential entry point, from remote laptops to cloud databases.
- Protect: We deploy a tailored mix of hardware, software, and protocols. This isn’t a one-size-fits-all solution; it’s a robust shield designed for your specific operational needs.
- Monitor: Security is a 24/7 job. We implement proactive surveillance and threat hunting to catch suspicious activity in real-time.
- Review: The digital world moves fast. We regularly update your strategy to combat emerging 2026 threats, ensuring your protection never goes stale.
The Importance of a Security Audit
An external audit is essential because it uncovers “blind spots” that internal teams often overlook. When you’re involved in the day-to-day running of a business, it’s easy to miss a legacy server or an unpatched piece of software. A professional cyber security assessment provides a fresh, expert perspective on your digital estate. This process informs a bespoke technology roadmap. Instead of guessing which tools you need, you’ll have a clear plan based on hard data. It’s about spending your budget where it will have the most significant impact on your safety.
Disaster Recovery and Incident Response
Having a plan is just as important as having the protection itself. Many people confuse “backup” with “disaster recovery,” but they’re very different concepts. A backup is a copy of your data; disaster recovery is the entire process of getting your business back online after a crisis. If a server fails or ransomware hits, you need to know exactly who does what and how long it will take to be operational again. We focus on testing your response plan regularly. This ensures that if the worst happens, downtime is kept to an absolute minimum, protecting your reputation and your bottom line. It’s this level of preparation that provides true peace of mind for North East business owners.
Ready to strengthen your business? Our award-winning team is here to help. Book a free cyber security consultation with a local expert today.
Why Partner with an Award-Winning IT Security Provider?
Choosing the right team to manage your cyber security services determines how well you sleep at night. It’s about finding a partner who understands that technical jargon doesn’t solve problems; proactive action does. We bring a “can-do” attitude to every complex challenge, ensuring that your systems don’t just survive but thrive. Our approach combines a national reach with the heart of a local partner, specifically designed to support UK SMEs. We deliver this protection through robust managed IT services, creating a seamless foundation for your business growth.
Technology moves fast, but your security shouldn’t be a source of constant stress. We believe a trusted expert should simplify the complex. When you face a technical hurdle, our team doesn’t look for excuses. We find solutions. This proactive mindset is what separates a standard vendor from a true partner. For UK SMEs, this relationship is vital. You need the scale of a national provider to handle modern threats, but you deserve the attention of a local team that understands the British business environment and regulatory landscape.
Award-Winning Excellence as a Standard
Quality isn’t a vague promise; it’s a proven track record. Being a multi-award-winning provider means we’ve consistently met rigorous standards for service, innovation, and reliability. This recognition reflects our commitment to excellence in every ticket we close and every network we secure. We’ve built strong alliances with global leaders like Microsoft, Cisco, and IBM to bring enterprise-grade protection to your doorstep. These partnerships ensure we’re always at the forefront of the latest cyber security services and technological breakthroughs.
This isn’t just about high-level strategy. Our dedicated helpdesk offers immediate peace of mind for those small, everyday security queries that can otherwise cause big delays. Whether it’s a suspicious email or a multi-factor authentication glitch, our experts are ready to help. You get the backing of global technology with the personal touch of a North East team that knows your name and your business goals.
- Direct Access: No gatekeepers, just expert engineers ready to solve problems.
- Global Standards: Tier-one partnerships that provide the best tools in the industry.
- Proven Results: Award-winning service that prioritises your uptime and safety.
Ready to Secure Your Business Future?
The shift from a simple service provider to a long-term technology partner changes everything. We don’t just fix what’s broken; we build what’s resilient. It starts with a simple conversation. We’d love to have a chat about your current security posture and where you want to take your business in 2026. This isn’t a high-pressure sales pitch. It’s an expert look at how to protect your hard work and ensure your team can work without fear of digital disruption. Speak to our award-winning team today for a tailored security review.
Secure Your Business Future in 2026 and Beyond
The digital landscape of 2026 demands more than just basic firewalls; it requires a culture of total resilience. By shifting from reactive fixes to a proactive 5-step framework, you’re not just protecting data. You’re securing your company’s reputation and long-term growth. Robust cyber security services are now the foundation of every successful UK enterprise. As a multi-award-winning IT provider based right here in the North East, Cornerstone Business Solutions brings the power of our partnerships with Microsoft, Cisco, and IBM directly to your doorstep.
We don’t believe in one-size-fits-all templates. We focus on bespoke strategies that keep you ahead of evolving threats. Our team provides proactive 24/7 monitoring to ensure you enjoy total peace of mind while you focus on what you do best. Don’t leave your digital assets to chance when expert help is just a conversation away. Book your bespoke cyber security audit with our award-winning team and let’s start building a safer, more resilient future for your business today.
Frequently Asked Questions
What are the most common cyber security services for UK businesses?
Managed firewalls, endpoint detection, and multi-factor authentication represent the most common defenses for UK firms. The 2024 Cyber Security Breaches Survey shows that 70% of medium businesses now prioritize these tools to block phishing and malware. We also focus on regular vulnerability scanning and employee awareness training to ensure your team becomes your strongest line of defense.
How much do managed cyber security services typically cost?
Costs depend on your specific infrastructure and the number of users you need to protect. Industry data from 2024 indicates that UK SMEs typically invest between £50 and £150 per user per month for comprehensive cyber security services. This proactive investment covers 24/7 monitoring and threat detection, which is significantly more cost-effective than the £1,100 average cost of a single breach for small firms.
Is my small business really a target for cyber criminals?
Small businesses are primary targets because they often lack the robust protection found in larger corporations. The Cyber Security Breaches Survey 2024 found that 50% of UK businesses experienced a breach or attack in the last 12 months. Criminals use automated bots to find any vulnerable entry point, meaning your size doesn’t protect you; only your security measures do.
What is the difference between IT support and cyber security services?
IT support focuses on keeping your systems operational and fixing day-to-day hardware or software issues. In contrast, cyber security services provide a specialized layer of defense dedicated to protecting your data from sophisticated threats. Think of IT support as the engine maintenance for your car, while cyber security is the high-tech alarm and tracking system that prevents theft.
How does Zero Trust security work in a practical business setting?
Zero Trust operates on the simple principle of “never trust, always verify.” In a practical office setting, this means every user and device must prove their identity before they can access any part of your network. We implement this through strict identity management and micro-segmentation, ensuring a single compromised password doesn’t give a hacker access to your entire business database.
Can cyber security services help with NIS2 or GDPR compliance?
Specialist security partners ensure your technical controls meet the strict legal requirements of GDPR and the 2024 NIS2 directive. We provide the encryption, access logs, and breach notification protocols required to keep you compliant. Since the ICO can issue fines up to £17.5 million or 4% of global turnover, these services act as a vital safeguard for your business reputation.
What should I look for when choosing a cyber security partner?
You should look for a partner with award-winning credentials and local North East roots who understands your specific regional challenges. It’s vital to choose a team that offers proactive monitoring rather than just reactive fixes. Check for certifications like Cyber Essentials Plus and ensure they offer a transparent roadmap that focuses on your long-term business resilience and peace of mind.
How often should my business undergo a cyber security audit?
You should conduct a full security audit at least once every 12 months to stay ahead of evolving digital threats. High-growth companies or those handling sensitive client data often benefit from quarterly reviews to catch new vulnerabilities. Regular audits identify gaps created by software updates or new hires, ensuring your defenses remain robust as your business continues to scale.
