What if your technology stopped being a source of stress and started being your biggest competitive advantage? For many local firms, IT often feels like a series of expensive fires to put out, especially with 50% of mid-sized UK businesses facing a cyber breach in the last year. It’s time to change that perspective. Strategic IT infrastructure planning for small business is the difference between a system that hinders your staff and one that drives your growth. As a dedicated local partner, we’ve seen how the right foundation turns IT from a reactive cost into a proactive engine for success.
We know the frustration of unpredictable monthly spend and the nagging fear that a single security flaw could halt your operations. You deserve a stable, “always-on” environment where your data is secure and your costs are predictable. This guide provides a clear roadmap to achieving exactly that. We’ll walk you through the 2026 UK regulatory landscape, including the Cyber Security and Resilience Bill, and show you how to navigate upcoming Microsoft 365 price changes. By the end, you’ll have the confidence to build a resilient, scalable foundation that protects your business and empowers your team to work without limits.
- Learn why shifting from reactive “break-fix” support to a proactive strategic partnership is essential for your organization’s resilience.
- Discover the core pillars of IT infrastructure planning for small business, including cloud solutions and the final UK PSTN switch-off.
- Identify the “silent tax” of slow systems. We’ll show you how proactive planning eliminates the high costs of unplanned downtime.
- Follow our five-step framework to audit your current digital landscape and resolve single points of failure.
- See how Cornerstone Business Solutions’ multi-award-winning approach provides the approachable, expert warmth your local business deserves.
What is IT Infrastructure Planning for Small Businesses?
Think of your technology as the digital backbone of everything you do. From the moment you open your email to the final backup of the day, your systems are working hard to keep your business moving. To understand the basics, we often look at What is IT Infrastructure as a combination of hardware, software, and network resources. For a local firm, this isn’t just “tech stuff.” It’s the very foundation of your service. Effective IT infrastructure planning for small business transforms these components from a messy collection of tools into a streamlined growth engine.
The Difference Between IT Support and IT Strategy
IT support is about the “now.” It’s the helpdesk fixing a printer or resetting a password. While essential, support alone won’t grow your business or drive digital transformation. IT strategy is about the “next.” It looks at where you want to be in twelve months and builds the path to get there. We use proactive system monitoring to stop issues before they even reach your desk. This keeps your staff productive and your operations smooth, ensuring your technology supports your goals rather than standing in the way.
Why Small Businesses Cannot Afford “Accidental” IT
Building a Resilient 2026 Technology Roadmap
A resilient roadmap isn’t just a list of hardware you want to buy. It’s a strategic shield that protects your operations from the unexpected. For 2026, effective IT infrastructure planning for small business rests on four critical pillars: Security, Cloud, Connectivity, and Continuity. When these elements work in harmony, your technology moves from being a source of friction to a driver of efficiency. You stop worrying about what might go wrong and start focusing on how much further your team can go.
One of the most urgent shifts for UK firms right now is the final move away from legacy systems. The UK’s old copper network is being phased out, making the transition to resilient VoIP telephone systems a necessity rather than a choice. Future-proofing your communications ensures you aren’t left behind when the final PSTN switch-off deadlines hit. By planning this transition now, you avoid the rush and ensure your business mobile and office lines remain crystal clear and fully integrated.
Surprise capital expenditure is the enemy of a healthy cash flow. We recommend aligning your hardware refresh cycles with your long-term financial planning. This prevents that sudden £2,000 bill when an old server finally gives up. Instead, you can spread costs and ensure your staff always have reliable, high-performance tools. In 2026, this also means adopting a “Zero Trust” security posture. With the Cyber Security and Resilience Bill now in force, even the smallest firms must verify every user and device. It’s about building a fortress around your data that remains invisible to your productive staff.
Cloud-First Strategy: Microsoft 365 and Azure
Your productivity hub should live where your people do: everywhere. Implementing a Microsoft 365 migration for business UK allows your team to collaborate securely from any location. By moving workloads to Azure, you eliminate the need for a noisy, expensive server room. We ensure your cloud environment is configured for maximum security and cost-efficiency, so you only pay for what you actually use. If you’re ready to modernize, we can help you start an expert IT roadmap session to plot your course.
Connectivity and Hybrid Work Infrastructure
Hybrid work is no longer a perk; it’s the standard. Your network must support seamless collaboration between the office and the home. This requires business-grade broadband that doesn’t buckle under the pressure of constant video calls. By integrating robust cloud solutions, you guarantee that your data is accessible and secure, no matter where your team logs in. This connectivity is the glue that keeps your modern business together.
The ROI of Strategic IT: Calculating the Cost of Doing Nothing
Ignoring your technology is a choice, but it’s an expensive one. Many owners view IT as a pure overhead; a necessary evil that drains the bank account every month. This perspective misses the “silent tax” that slow systems levy on your business every single day. When a staff member waits for a spinning wheel on their screen, or a slow network delays a customer quote, your profitability takes a hit. IT infrastructure planning for small business is about identifying these leaks and plugging them before they drain your margins.
Quantifying Downtime and Productivity Gaps
Downtime is easier to calculate than you might think. To find your true hourly cost of a system outage, use this simple formula: (Number of Employees x Average Hourly Rate) + Lost Revenue per Hour. For a firm with 15 staff, a single morning of downtime can easily cost over £2,000 in wasted wages and missed opportunities. By partnering with experts for managed IT services, you gain a measurable return on investment through increased uptime. Remember, “cheap” IT often ends up being the most expensive option over a three-year cycle when you factor in emergency repairs and lost productivity.
Security as a Foundation for Business Continuity
Peace of mind is perhaps the most valuable ROI of all. Knowing that your systems have 24/7 proactive threat monitoring allows you to sleep better at night. Our cyber security services act as the ultimate insurance for your hard-earned reputation. Beyond protection, a strong security posture is now a commercial requirement. With the Cyber Security and Resilience Bill tightening standards, having a certified, secure infrastructure helps you win larger contracts and pass rigorous supply chain audits with ease. Proactive IT infrastructure planning for small business ensures you’re always ready for the next big opportunity.

5 Steps to Building Your IT Infrastructure Plan
Creating a plan doesn’t have to be overwhelming. It’s about taking logical steps that lead to a massive improvement in your daily operations. Effective IT infrastructure planning for small business provides a clear map for your growth, ensuring you never feel stuck with outdated tools or vulnerable systems. By following a structured process, you move from “making do” to “moving forward” with total confidence.
- Step 1: Conduct a comprehensive audit. You can’t plan for the future without knowing exactly where you stand today. This involves more than just counting laptops; it’s about understanding how data flows through your business.
- Step 2: Identify business-critical risks. Locate your single points of failure. This could be an aging server, a single internet connection, or a lack of off-site backups. Identifying these gaps now prevents a crisis later.
- Step 3: Define your technology goals. Where do you want to be in 12, 24, and 36 months? Your infrastructure should scale alongside your ambitions, whether you’re adding five new staff or opening a second location.
- Step 4: Establish a sustainable budget. Shift your focus from “how much does this cost today” to “what is the total cost of ownership.” A sustainable budget avoids surprise bills and ensures your tech remains a reliable asset.
- Step 5: Select a partner who specialises in SME growth. You need more than a vendor; you need a dedicated partner who understands the local landscape and treats your success as their own.
The Audit: Looking Beyond the Servers
A true audit starts with your people. We look for staff pain points where technology is currently slowing them down. This might be a slow login process or a clunky remote access system that frustrates your hybrid workers. We also review your software licensing. Many firms overpay for unused seats or “zombie” subscriptions that drain the budget. Finally, we check your compliance against UK standards like Cyber Essentials. This government-backed scheme is a vital baseline for any firm looking to prove their security credentials to clients and insurers alike.
Aligning Tech Spend with Your Growth Ambitions
Successful planning moves you away from unpredictable capital expenditure and toward a fixed-fee it company solutions model. This makes your monthly outgoings predictable and manageable. We help you prioritise investments based on business impact rather than technical novelty. It’s not about having the newest gadget; it’s about having the right tool for the job. Regular strategy reviews are essential to keep your plan on track. As your business evolves, your technology should evolve with it. If you’re ready to build a foundation that lasts, speak with our local team to begin your journey.
Why Cornerstone is the Trusted IT Strategy Partner for UK SMEs
Choosing a partner for your technology is one of the most important decisions you’ll make for your firm’s future. At Cornerstone, we’ve built our reputation on a multi-award-winning approach to proactive technology management. We don’t just offer support; we provide a dedicated long-term partnership. Our team blends professional authority with an approachable, regional warmth that makes us feel like a part of your own office. We believe that IT infrastructure planning for small business should be a collaborative journey, not a series of one-off transactions.
We focus on the long game. While other providers might focus on quick fixes, we look at how your infrastructure will support your growth over the next three to five years. This proactive attitude ensures your systems remain resilient against emerging threats and ready for new opportunities. We frame every technical solution within the context of your business continuity and emotional security, providing a foundation you can truly rely on.
Your Virtual CTO: Expert Advice Without the Executive Salary
Imagine having the insight of a seasoned Chief Technology Officer without the burden of an executive salary. We act as an extension of your own team, driving your technology forward with clear, benefit-driven advice. We speak the language of business, not just “tech-speak,” so you’ll always understand the “why” behind our recommendations. Through regular strategic reviews, we ensure your IT infrastructure planning for small business always matches your current ambition. We keep your systems aligned with your goals, helping you scale efficiently while avoiding expensive technical debt.
Start Your 2026 Strategy Conversation Today
The best time to plan your infrastructure is before you think you need to. Waiting for a system failure or a security breach to act is a risk your business doesn’t need to take. We invite you to an informal chat about your business goals and the challenges you’re currently facing. Whether you’re worried about the upcoming Cyber Security and Resilience Bill or need to modernize your hybrid work setup, we’re here to help. Our team is ready to listen and provide a reassuring, expert perspective on your digital future.
Ready to build a roadmap for growth? Let’s have a conversation.
Secure Your Business Future Today
Your technology should be a source of confidence, not a constant worry. By shifting from reactive fixes to proactive IT infrastructure planning for small business, you ensure your organization is ready for the challenges of 2026. You’ve seen how a resilient roadmap protects your staff from downtime and how a clear audit can reveal hidden costs. This isn’t just about hardware. It’s about building a stable foundation that allows your local firm to compete with the giants.
As a multi-award-winning IT service provider, we specialize in bespoke UK SME technology solutions. Our strong partnerships with global leaders like Microsoft, IBM, and Cisco mean we bring world-class reliability right to your doorstep. We’re more than just a vendor; we’re your dedicated long-term partner. We take the stress out of compliance and security so you can focus on what you do best.
Ready to transform your IT into a growth engine? Book your 2026 IT strategy review with our award-winning team. Let’s work together to make your business systems “always-on” and fully compliant. We look forward to helping your business thrive.
Frequently Asked Questions
What exactly is included in an IT infrastructure plan for a small business?
A comprehensive plan acts as your digital blueprint. It includes a detailed inventory of your hardware, a review of your software licensing, and a clear map of your network infrastructure. We also build in robust security protocols and disaster recovery steps. This ensures every part of your technology, from your business VoIP to your cloud storage, works together to support your daily operations and long-term goals.
How much does IT infrastructure planning typically cost for a UK SME?
We only have 15 employees; are we too small for a formal IT strategy?
How often should a small business review its technology roadmap?
We recommend a formal review at least once every quarter. Technology moves fast, and your business goals can shift just as quickly. Regular check-ins ensure your IT infrastructure planning for small business remains aligned with your ambitions. These reviews also help you stay ahead of new UK regulations, such as the Cyber Security and Resilience Bill, ensuring your organization remains compliant and secure as the landscape evolves.
What is the difference between an IT audit and an IT strategy plan?
An audit is a snapshot of your technology as it exists today. It identifies aging hardware, security vulnerabilities, and software that needs updating. An IT strategy plan is the map that shows you where you’re going. While the audit finds the problems, the strategy provides the long-term solutions and the timeline to implement them. You need the audit to understand your starting point, but you need the strategy to reach your destination.
Can a better IT infrastructure plan help reduce our monthly technology bills?
How long does it take to develop and implement a full technology roadmap?
Creating the initial roadmap usually takes between two and four weeks. This allows us to conduct a thorough audit and understand your specific business challenges. Implementation is typically a phased process to avoid disrupting your staff. You might see security improvements within days, while larger projects, like migrating to a new server-less cloud environment, are carefully managed over several months to ensure a smooth and seamless transition.
What are the first signs that my business needs a formal IT infrastructure plan?
The most common red flag is a feeling of being “reactive” rather than “proactive.” If you’re constantly dealing with system slowdowns, unpredictable IT spend, or staff frustration, your current setup is likely struggling. Another sign is “accidental” growth, where you’ve added tools over time that don’t talk to each other. Moving to formal IT infrastructure planning for small business will replace this technical friction with a reliable, “always-on” environment.
Fully Managed IT Services for UK Businesses: The 2026 Strategic Guide
Your technology shouldn’t be an expensive light switch that you simply hope works when you flip it. In 2026, it needs to be the engine driving your business forward. We understand the frustration of unpredictable costs and technical glitches that stall your team just when things get busy. With the UK managed services market reaching over $23 billion in 2025, it’s clear that more companies are seeking stability through professional partnerships. You’re likely tired of jargon while trying to figure out how the Cyber Security and Resilience Bill impacts your compliance. Choosing fully managed IT services for UK businesses is no longer just about fixing laptops; it’s about building a foundation for resilience.
This guide explains how to transition your IT from a cost centre to a strategic growth engine while securing your business against modern threats. We’ll show you exactly what to expect when you move to a proactive model that prioritizes your stability and peace of mind. You’ll learn how a dedicated regional partner simplifies complex cloud solutions and network infrastructure so you can focus on your goals. We’re proud to support our local business community with the clarity and expertise you deserve. Let’s explore how the right support keeps your operations running smoothly and your data safe.
Key Takeaways
- Move beyond the outdated break-fix model by embracing a proactive partnership that fixes problems before they impact your team.
- Discover how fully managed IT services for UK businesses use “Security by Design” to keep your company compliant and resilient against evolving digital threats.
- Uncover the hidden costs of downtime to see how a strategic IT investment pays for itself through improved productivity and reliability.
- Learn the essential criteria for selecting a technology partner, from checking for industry awards to verifying ISO accreditations.
- Explore how a dedicated regional expert can turn your complex technology into a simple, scalable engine for your business growth.
What are Fully Managed IT Services for UK Businesses?
Imagine your technology just worked. No sudden outages, no frantic calls to a technician who doesn’t know your name, and no surprise invoices at the end of the month. This is the reality of a proactive partnership. Understanding What are Managed Services is the first step toward transforming your operations. Essentially, fully managed IT services for UK businesses represent a commitment where an expert provider takes total responsibility for your digital environment. It moves your technology away from reactive firefighting and toward a stable, strategic foundation that supports your long-term goals.
In 2026, the tech landscape has shifted significantly. We’ve moved beyond dusty server rooms in the back office to complex hybrid cloud environments. This modern setup requires constant monitoring and a clear roadmap to ensure your systems remain efficient and secure. You gain peace of mind knowing a team is looking ahead, identifying potential issues before they cause a second of downtime. It’s about having a dedicated partner who simplifies the technical details so you can focus on running your business.
The Break-Fix Model vs. Fully Managed IT
The “Break-Fix” model is a cycle of frustration and hidden costs. Something fails, productivity stops, and you pay high emergency rates to fix a problem that should’ve been prevented. This approach makes budgeting impossible and keeps your business in a defensive, reactive state. You’re essentially waiting for disaster to strike before taking action, which is a risky way to manage your network infrastructure.
The “Managed” cycle focuses on prevention and continuous improvement. Through constant monitoring and regular maintenance, we ensure your systems stay healthy and perform at their best. You benefit from flat-fee budgeting, which removes the fear of unexpected technical bills. Managed IT is the externalisation of your entire IT department for a predictable monthly fee.
Why UK Businesses are Making the Switch in 2026
Modern work is more complicated than ever. With hybrid teams spread across different regions and a massive increase in SaaS applications, managing your digital footprint is a tall order. Small in-house teams often find themselves overwhelmed by sophisticated cyber threats and the constant need for software updates. They simply don’t have the time to be both a helpdesk and a strategic director.
The Core Pillars of a Modern Managed Service
A true technology partnership isn’t a buffet where you pick and choose individual fixes. It’s a cohesive ecosystem designed to keep your business running without interruption. To be effective, fully managed IT services for UK businesses must encompass three non-negotiable pillars: security, continuity, and communication. We build every solution on a foundation of “Security by Design.” This means protection isn’t an afterthought or a plugin. It’s baked into your network infrastructure and cloud environment from day one, ensuring that every piece of hardware and software contributes to your overall safety.
As you evaluate your current setup, it helps to Determine if Managed IT is Right for Your Business based on your specific growth goals. For many, the integration of Business VoIP and Business Mobile into the IT ecosystem is the true turning point. It ensures your team stays connected whether they are in the office or working remotely across the country. This unified approach eliminates the friction of managing multiple providers and creates a more reliable communication stream for your clients.
Advanced Cyber Security and Compliance
The regulatory landscape in 2026 is stricter than ever. The Cyber Security and Resilience (CS&R) Bill has expanded oversight, making compliance a daily operational task rather than a yearly check-box exercise. Our approach includes 24/7 threat monitoring, phishing simulations, and robust multi-factor authentication (MFA) to keep you ahead of these mandates. We act as your compliance shield, ensuring your data handling meets the latest UK standards. You can explore our Cyber Security Services for a deeper look at how we build this resilience into your daily operations.
Seamless Cloud Solutions and Microsoft 365
Cloud optimization is the priority for businesses this year. We help you move beyond simple storage to true performance management. Whether it’s managing a Microsoft 365 migration for business UK or deploying Azure virtual desktops, we ensure zero data loss and maximum uptime. Our team focuses on FinOps to make sure you aren’t overspending on resources you don’t need. This creates a flexible, national workforce that can access critical files securely from any location. If you’re wondering how these pillars fit your specific needs, starting a conversation with a local expert can clarify the best path forward for your digital growth.

Calculating the ROI: Beyond the Monthly Fee
When calculating the return on investment for fully managed IT services for UK businesses, the conversation must shift from “what does it cost?” to “what does it save?” It’s a common question we hear from business owners who are wary of adding another line item to their monthly expenses. However, viewing technology as a mere utility, like water or electricity, overlooks its power as a strategic asset. A proactive partnership doesn’t just fix problems; it eliminates the financial drain caused by inefficient systems and unexpected failures. By moving from a capital expenditure (CAPEX) model to a predictable operating expense (OPEX), you gain the clarity needed for long-term financial forecasting.
The Cost of Doing Nothing
The true price of an outdated “Break-Fix” approach is often hidden until disaster strikes. Consider a hypothetical scenario: a 20-person firm suffers a total system outage lasting just four hours. If the average hourly wage is £25, you’ve already lost £2,000 in staff productivity alone. This doesn’t even account for lost sales, missed deadlines, or the long-term damage to your professional reputation. Contrast this with a proactive plan that monitors your systems and applies patches before a failure occurs. The cheapest IT support is the one that prevents the problem from ever occurring.
Technology as a Growth Driver
Efficient systems do more than just stay online; they accelerate your entire workflow. When your team isn’t battling slow connections or software glitches, their job satisfaction and output naturally increase. We act as your Virtual CTO, guiding you toward IT company solutions that are designed to scale alongside your ambitions. This gives your SME access to enterprise-grade tools and security on a manageable budget. By aligning your technology with your business goals, you turn your digital environment into a competitive advantage that helps you outpace larger, less agile competitors.
How to Choose the Right IT Partner in the UK
Selecting a technology partner is a decision that impacts every facet of your daily operations. It is not just about who can reset a password the fastest or who has the lowest price. When you evaluate fully managed IT services for UK businesses, you are looking for a team that acts as a natural extension of your own staff. This relationship thrives on approachable communication and a proactive attitude. Technical skills are the entry requirement, but cultural fit and a genuine interest in your success are what truly drive a long-term partnership.
Your Service Level Agreement (SLA) should offer absolute clarity rather than just vague uptime claims. While many providers promise “99.9% availability,” you need an agreement that defines exactly how they support your business continuity. A transparent SLA outlines clear response times and responsibilities without burying them in technical jargon. It should feel like a foundational promise of stability and emotional security for your team.
The Evaluation Checklist for Business Leaders
- Does the provider offer a bespoke roadmap or a one-size-fits-all package? Your business is unique. Your technology strategy must be tailored to your specific goals and network infrastructure.
- Are they partners with global brands like Microsoft, Cisco, or IBM? High-level partnerships ensure your provider has direct access to the latest tools, training, and vendor support.
- Do they have a proven track record in your specific sector? Experience in your industry means they already understand your common challenges and the software you rely on most.
Red Flags to Avoid
- The “Fix-Only” Mentality: Be wary of providers who only talk about repairing things when they break. If they aren’t discussing long-term strategy, they aren’t truly managing your IT.
- Static Contracts: Avoid long-term commitments that do not include regular account reviews. You need a partner that adapts their services as your company scales.
- Hidden Extras: Watch out for contracts that charge extra for basic tasks. Ensure your monthly fee covers unlimited helpdesk support so you can budget with total confidence.
If you are ready to move away from technical headaches and toward a strategic partnership, speak with our award-winning team today to see how we can support your growth.
The Cornerstone Difference: Award-Winning Partnership
We believe technology should be a quiet, powerful force supporting your ambitions, not a constant source of stress. As a multi-award-winning leader in the UK IT space, Cornerstone Business Solutions brings a unique perspective to fully managed IT services for UK businesses. Our philosophy is built on “Regional Warmth, National Reach.” This means you get the sophisticated, enterprise-grade capabilities of a national provider delivered with the friendly, accessible face of a local team who genuinely cares about your success. We don’t just fix PCs; we look at your entire digital ecosystem to ensure every component helps you thrive.
Moving away from transactional, “per-ticket” support allows us to act as a dedicated long-term partner. We invest time in understanding your specific operational challenges and your community roots. This collaborative approach ensures our experts are always aligned with your goals. We provide the clarity and stability you need to make bold business decisions, knowing your foundation is secure. By choosing fully managed IT services for UK businesses, you are choosing a team that values your uptime and your emotional security as much as you do.
Bespoke Technology Solutions
One-size-fits-all packages often lead to wasted spend and technical bottlenecks that hinder your progress. We specialise in creating custom cloud solutions tailored to your unique objectives and network requirements. By partnering with world-leading technology brands, we deliver robust systems that are both scalable and secure. Our commitment to clear, jargon-free communication means you’ll always understand the “why” behind our recommendations. We translate complex infrastructure into plain English, putting you back in control of your technology assets.
Ready to Transform Your IT?
The journey from tech-frustration to tech-enabled growth starts with a single decision to change your perspective. You’ve seen how a proactive model can secure your data, stabilise your costs, and drive your productivity. Cornerstone Business Solutions is ready to act as a seamless extension of your own organisation, providing the proactive care and strategic oversight required in 2026. We invite you to step away from the stress of recurring glitches and unpredictable invoices. Let’s start a conversation about your future roadmap and build a technology strategy that actually works for you.
Take the Next Step Toward Digital Resilience
You’ve explored how transitioning from a reactive “break-fix” mindset to a proactive partnership turns your technology into a strategic growth engine. By prioritising “Security by Design” and staying ahead of the 2026 Cyber Security and Resilience Bill, you protect your team from the hidden financial drain of downtime. Choosing fully managed IT services for UK businesses through Cornerstone Business Solutions ensures you have the stability needed to scale with confidence. We combine national-level expertise with the approachable, regional warmth that defines our community-focused approach.
Our status as a multi-award-winning provider is backed by strong partnerships with industry giants like Microsoft, IBM, and Cisco. These connections allow us to deliver bespoke technology solutions that are as unique as your business goals. It’s time to move beyond transactional tech support and embrace a partnership built on trust and reliability. Book a friendly, no-obligation IT review with our award-winning team today to define your roadmap for the years ahead. Cornerstone Business Solutions is ready to help your business thrive in an increasingly digital world.
Frequently Asked Questions
What is included in fully managed IT support?
Fully managed support covers the total management of your digital environment. This includes proactive Managed IT Support, Microsoft 365 management, robust Cyber Security, and the maintenance of your network infrastructure. We take responsibility for everything from software updates to disaster recovery, ensuring your systems remain stable and efficient without requiring your daily intervention.
How much do managed IT services typically cost for a UK business?
Pricing is usually structured as a predictable monthly fee based on the number of users and the complexity of your systems. This model helps you move from unpredictable capital expenses to a stable operating budget. While costs vary between providers, you should look for a transparent agreement that covers unlimited helpdesk support and strategic reviews to ensure you receive the best value for your investment.
Can a managed IT provider help with cyber security compliance like Cyber Essentials?
Yes, helping you achieve and maintain certifications like Cyber Essentials is a core part of a modern partnership. We act as your compliance shield, ensuring your systems meet the latest UK standards and the requirements of the 2026 Cyber Security and Resilience Bill. Our team implements the necessary controls, from multi-factor authentication to secure cloud solutions, to keep your data protected and your business compliant.
Will we lose control of our IT systems if we outsource?
You retain full ownership and strategic oversight of your technology at all times. We act as an extension of your own team, providing the expert hands and eyes needed to manage the technical details while you make the final business decisions. Our goal is to empower you with better data and more reliable systems, giving you more control over your company’s growth rather than less.
How long does it take to switch to a new managed IT provider?
The transition typically takes between 30 and 90 days, depending on the size of your network infrastructure. We follow a structured onboarding process that includes a deep audit of your current systems and a seamless handover from your previous provider. This careful approach ensures there is no disruption to your daily operations while we implement your new bespoke technology roadmap.
Do managed IT services include hardware and equipment?
We provide full IT Hardware procurement as part of our comprehensive service. This means we can source, configure, and install everything from high-performance laptops to complex servers and networking gear. By managing your hardware lifecycle, we ensure that your team always has access to reliable, up-to-date equipment that is fully compatible with your cloud solutions.
What happens if we have an emergency outside of normal business hours?
You should check your specific Service Level Agreement (SLA) to understand the support hours available to your business. While we focus on proactive monitoring to catch and resolve issues before they become emergencies, we understand that technical challenges can arise at any time. A reliable partner will always provide clear instructions on how to access help when you need it most.
Is managed IT support suitable for very small businesses or just large ones?
Managed IT is designed for businesses of all sizes, particularly SMEs that need enterprise-grade technology on a manageable budget. Choosing fully managed IT services for UK businesses allows smaller firms to compete with larger rivals by using the same sophisticated tools and security. Our solutions are fully scalable, meaning your technology grows alongside your company without the need for a massive internal IT department.
In-House vs Outsourced IT Support: A 2026 Cost Analysis for UK Businesses
Would you pay £65,000 for a single IT generalist when you could access an entire team of specialists for a third of that price? By January 2026, the cost of a competent internal hire has climbed to between £45,000 and £65,000 once you factor in National Insurance and pension contributions. It’s a heavy price to pay for one person who still needs holidays, sick leave, and constant training. This 2026 in-house vs outsourced IT support cost analysis reveals why many North East businesses are moving away from the traditional hiring model to find better value and more reliable protection.
We know that managing technology often feels like a constant battle against recruitment headaches and rising cyber security threats. You want predictable monthly spending and the peace of mind that comes from award-winning expertise. This guide delivers a full financial and strategic breakdown to help you choose the model that actually supports your growth. We will explore the hidden costs of internal teams, from £5,000 annual training budgets to the £200,000 per hour risk of downtime. We also show you how a proactive partnership delivers the robust security your insurance requires. Let’s get into the numbers so you can make an informed decision for your organization’s future.
Key Takeaways
- Compare the actual cost of a £65,000 internal hire against the predictable monthly investment of an award-winning managed service provider.
- Identify the “hidden 30%” of internal IT spending, including National Insurance and the recruitment overheads that often catch businesses off guard.
- Use our 2026 in-house vs outsourced IT support cost analysis to determine which model delivers the best ROI for your specific headcount.
- Learn how to eliminate “Key Person Risk” and gain access to a full suite of experts for cyber security, cloud solutions, and strategic planning.
- Discover the framework for choosing a model that provides long-term peace of mind and supports your business growth without technical stagnation.
The 2026 IT Landscape: Why the In-House vs Outsourced Debate Matters
Choosing between these models requires a balance of three critical factors: cost, control, and capability. While having a dedicated person in the office feels reassuring, the sheer breadth of knowledge required today is staggering. One person cannot be an expert in Microsoft 365, advanced cloud infrastructure, and 24/7 cyber security monitoring all at once. We believe that technology should provide peace of mind, not a constant source of recruitment stress. This analysis helps you find that balance, ensuring your IT investment delivers a genuine return rather than just becoming a line item on a balance sheet.
The Evolution of IT Support Expectations
The old “IT guy in the basement” model is officially obsolete. In 2026, your team expects 24/7 uptime and seamless remote access from any location. If your systems go down for even an hour, the financial fallout for a UK firm can reach £200,000 depending on the sector. This “always-on” culture means IT has moved from a back-office expense to a front-line driver of efficiency. Our guide to managed IT services Teesside explores how local businesses are adapting to these higher stakes by moving toward proactive, rather than reactive, support models.
Defining the Models: DIY vs. Managed Partnership
Understanding the terminology is the first step toward a smart decision. The business practice of outsourcing involves hiring an external provider to handle your technology needs. Here is how the three main models look for a modern North East business:
- In-house IT: You hire internal employees. This offers direct control and deep company-specific knowledge; however, it comes with high fixed overheads, pension contributions, and significant recruitment challenges.
- Outsourced IT: You partner with an award-winning Managed Service Provider (MSP). This provides access to a full team of experts for a predictable monthly fee, eliminating the need for internal training and recruitment.
- Hybrid or Co-managed: This is often the “best of both worlds” for larger SMEs. Your internal IT manager handles day-to-day helpdesk tasks while a proactive partner manages heavy-duty security, disaster recovery, and infrastructure.
The True Cost of In-House IT Support in 2026
Calculating the price of an internal team often starts with a single salary figure. However, a realistic in-house vs outsourced IT support cost analysis for 2026 must look far beyond the basic pay packet. While a generalist might command a salary between £30,000 and £45,000, a truly competent engineer capable of managing modern infrastructure now costs between £45,000 and £65,000. These figures reflect the intense competition in the UK managed services market, where a persistent skills gap continues to drive wage inflation across the technology sector.
The Salary Trap: Why One Person is Never Just One Salary
Hiring for IT in 2026 often forces SMEs into a difficult choice. You can hire a junior technician for £35,000, but they may lack the expertise to handle high-level strategic planning or complex cyber security audits. To get that level of seniority, you’ll likely need to pay upwards of £55,000 for a mid-level professional. Even then, you are only buying the knowledge of one individual. If they fall ill or take a holiday, your business is left vulnerable. This “Key Person Risk” can lead to expensive downtime that far outweighs the cost of a proactive partnership.
Continuous Professional Development (CPD) Costs
Technology moves fast. To keep an internal staff member effective, you must invest £2,000 to £5,000 every year in certifications for Microsoft 365, Azure, or Cisco. Without this, your team’s skills will stagnate, leaving your business behind the curve. You also need to provide the tools for them to do the job. Essentials like remote monitoring (RMM), ticketing systems, and security software add another £3,000 to £8,000 to your annual overheads per technician.
The Total Cost of Ownership for a single competent IT hire in 2026 averages between £75,000 and £95,000 after combining salary, statutory contributions, recruitment amortisation, and essential software licensing. If these numbers feel daunting, it might be time to chat with a local expert about a more predictable, award-winning model that scales with your growth.

Financial Analysis of Outsourced Managed IT Support
Switching focus to the other side of our in-house vs outsourced IT support cost analysis, we see a model built for total predictability. Outsourcing replaces the volatile expenses of recruitment and training with a clear, per-user monthly fee. For a typical 20-user business in the UK, fully managed support costs between £1,100 and £1,700 per month. That totals roughly £13,200 to £20,400 per year. Compare that to the £75,000 minimum total cost of a single in-house hire we discussed earlier. You’re getting an entire department of experts for less than a third of the price of one person.
Scalability is another massive financial win for North East firms. If your team grows by five people tomorrow, your costs increase by a fixed, known amount. If you downsize, your bill drops immediately. You don’t have to worry about the £5,000 to £10,000 recruitment fees or the headache of interviewing. We handle the talent hunt and the continuous training, so you don’t have to. It’s a seamless way to ensure your business always has the right level of support without the burden of fixed overheads or employer’s National Insurance.
The Managed Service Advantage: Beyond the Helpdesk
A proactive partnership offers far more than just fixing what’s broken. Our cyber security services are built into the model, providing robust protection that satisfies modern insurance requirements. You get 24/7/365 monitoring without the massive overtime bills or holiday cover issues associated with internal staff. Specialists also manage your cloud solutions more efficiently, ensuring you aren’t overpaying for licenses or storage you don’t need. It’s award-winning expertise that keeps your business moving.
Comparing the Capital Expenditure (CapEx) vs. Operational Expenditure (OpEx)
CFOs generally prefer the Operational Expenditure (OpEx) model because it keeps cash flow steady. You avoid the “emergency spend” cycle where an unmanaged server failure leads to a sudden £10,000 bill. Instead, you pay a consistent monthly rate that covers maintenance and upgrades. Our team also leverages existing partnerships with giants like Microsoft and Cisco. This means you benefit from enterprise-level tools and pricing that are usually out of reach for smaller firms. It’s about getting the best technology for your business while maintaining total financial control and peace of mind.
The Efficiency Gap: Opportunity Costs and Risk Factors
Direct expenses like salaries and software licenses are easy to track, but the hidden costs of inefficiency often hit harder. A thorough in-house vs outsourced IT support cost analysis must weigh the financial impact of “Key Person Risk.” When your internal IT manager is on holiday, ill, or simply busy with a basic helpdesk ticket, who handles a critical system failure? For many North East businesses, this single point of failure creates a dangerous bottleneck that stalls productivity and threatens growth.
There is also the “Breadth vs Depth” problem to consider. In 2026, it is practically impossible for one person to stay expert in cloud infrastructure, hardware maintenance, and the latest cyber security protocols simultaneously. Internal staff often fall into a “best effort” support cycle. In contrast, a proactive partnership with an award-winning team provides guaranteed Service Level Agreements (SLAs). You aren’t just buying time; you are buying a commitment to performance and 24/7 availability that a single hire simply cannot match.
The Cost of Downtime: A Proactive vs. Reactive Comparison
Downtime is a silent profit killer. Recent data shows that IT failures cost UK businesses between £4,000 and £200,000 per hour depending on their sector and size. If your internal team is reactive, they only start working once the damage is done. Our proactive monitoring identifies and resolves vulnerabilities before they impact your bottom line. This level of oversight provides the peace of mind that comes from knowing your network is being watched by specialists who never take a day off. It turns IT from a source of stress into a foundation for business continuity.
Cyber Security and Compliance Risks
The landscape of digital threats is more hostile than ever in 2026. Data breaches now carry heavy financial penalties and can destroy a local brand’s reputation in days. Implementing robust it company solutions ensures your business remains compliant with strict regulations like NIS2 and Cyber Essentials. Managing these requirements internally is a massive administrative burden that often leads to corners being cut.
Professional IT management naturally reduces your cyber insurance premiums by proving to underwriters that your infrastructure is managed to enterprise standards. If you want to stop worrying about the next big threat and start focusing on your business, it’s time to chat with our local experts about a tailored support plan.
The Verdict: Which Model Wins for Your Business?
Choosing the right path depends on your specific scale and long-term goals. Our in-house vs outsourced IT support cost analysis shows that for the majority of UK SMEs, the decision comes down to the balance between overhead and expertise. If you are a large enterprise with over 500 users and highly bespoke legacy systems, an internal team might offer the deep, singular focus you need. However, for high-growth firms and security-conscious sectors, the managed model is almost always the superior choice for both ROI and reliability.
The data from January 2026 is clear. At the 20-user mark, outsourcing your technology needs costs roughly a third of a single in-house hire. Even at 50 users, where costs begin to equalize, the outsourced model still wins on value. You aren’t just paying for a person to sit at a desk; you are buying access to an award-winning department of specialists. This eliminates the “Efficiency Leak” where your business pays premium salaries for basic helpdesk tasks while strategic projects and cyber security fall by the wayside.
Making the Transition: From Stress to Strategy
Moving from a reactive, stressed IT environment to a proactive strategy starts with an honest audit of your current spend. Look beyond the obvious invoices. Calculate the time your management team spends on recruitment and the cost of every hour your systems were offline in the last twelve months. When you present these figures to your stakeholders, the conversation shifts from “what does this cost” to “what is this costing us to ignore.” Finding a partner with a local feel and national-level capabilities ensures you get the personal touch of a North East team with the robust infrastructure of a major provider.
Cornerstone: Your Award-Winning IT Partner
At Cornerstone, we believe technology should be a foundational element of your peace of mind. We blend professional authority with the approachable warmth of our North East roots to create a partnership that feels like an extension of your own team. Our proactive monitoring and tailored cloud solutions ensure your business stays ahead of the curve without the recruitment headaches or unpredictable break-fix bills. We are proud of our award-winning status, but we are even prouder of the success our clients achieve through reliable, secure technology.
Ready for a chat about your IT strategy? Contact our expert team today.
Secure Your Business Future with a Smarter IT Strategy
Your technology should be the engine of your growth, not a source of constant financial worry. This in-house vs outsourced IT support cost analysis has shown that while a £65,000 internal hire offers direct control, it cannot match the collective depth of an entire department. You gain access to specialists in cyber security, cloud solutions, and network infrastructure for a fraction of the cost of a single senior employee. It’s about moving from a reactive “break-fix” mindset to a proactive strategy that protects your bottom line.
As a multi-award-winning IT services provider with deep North East roots, we provide the proactive 24/7 monitoring you need to avoid that £200,000 per hour downtime risk. Our strong partnerships with Microsoft, IBM, and Cisco ensure your business uses enterprise-level tools that stay current with 2026 standards. We don’t just fix computers; we build the digital foundation your organization needs to scale securely and efficiently.
Book a free IT cost-analysis chat with our award-winning team today to find your efficiency leak. We look forward to helping your business achieve total peace of mind and long-term success.
Frequently Asked Questions
Is it cheaper to outsource IT or hire in-house in 2026?
Outsourcing is significantly more cost-effective for the vast majority of UK SMEs. Our in-house vs outsourced IT support cost analysis shows that a 100-user business typically invests between £60,000 and £90,000 per year for a full team of specialists. Hiring an equivalent internal team would require at least three staff members, likely pushing your annual expenditure well over £150,000 once you include all employer contributions and overheads.
What are the hidden costs of hiring an internal IT manager?
Beyond the base salary, you must budget for a 13.8% Employer National Insurance contribution and at least 3% for pension auto-enrolment. There are also recruitment fees that often reach 20% of the starting salary and an annual training budget of £2,000 to £5,000 to keep their skills current. You also pay for the software tools they need, which can cost your business an additional £8,000 every year.
Can a managed IT service provider really understand my specific business needs?
A true partnership model ensures your provider understands your operations as deeply as any internal hire. We use regular strategic reviews and on-site visits across the North East to align your technology with your specific growth goals. It’s about building a long-term relationship where we act as your trusted local experts, not just a distant helpdesk.
What happens to my existing IT staff if I decide to outsource?
You don’t have to choose one or the other; many firms opt for a co-managed approach. Your existing staff can focus on high-value internal projects while we handle the 24/7 monitoring and helpdesk tickets. If you decide to move fully to an outsourced model, we can help you navigate the TUPE regulations to ensure a smooth and professional transition for everyone involved.
How do outsourced IT costs scale as my business grows?
Costs scale linearly on a per-user basis, which gives you total budget clarity as you expand. For a 50-user business in 2026, the monthly investment typically ranges from £2,750 to £4,250 depending on the level of support required. This flexibility means you can add or remove users instantly without the stress of recruitment or the risk of being overstaffed during quieter periods.
Is outsourced IT support as responsive as having someone in the office?
Outsourced support is often more responsive because you have an entire team of award-winning experts available at all times. An internal hire might be stuck in a meeting, off sick, or on holiday when a crisis hits. Our proactive monitoring systems identify and fix most issues before your team even notices them, ensuring your productivity never skips a beat.
Does outsourcing IT help with cyber security insurance requirements?
Yes, professional management is now a standard requirement for most 2026 cyber insurance policies. Insurers want to see that your business has robust disaster recovery plans and proactive security monitoring in place. Partnering with an expert team ensures you meet these strict compliance standards, which often helps in securing coverage and potentially reducing your premiums.
What is co-managed IT support and is it right for me?
Co-managed IT is a hybrid model where we support your existing internal IT manager rather than replacing them. It’s a great fit for businesses with 50 or more staff that need extra help with specialized areas like cloud solutions or complex network infrastructure. This model typically costs between £30 and £80 per user per month and provides your internal team with the tools and backup they need to succeed.
Signs You Need to Outsource Your IT: The 2026 Strategic Guide for UK Businesses
With 43% of UK businesses reporting a cyber security breach in the last 12 months, the cost of “getting by” with a struggling tech setup has never been higher. When a single incident now averages a £57,900 financial loss for limited companies, you can’t afford to ignore the clear signs you need to outsource your IT. Perhaps your in-house staff is buried under minor helpdesk tickets, or you’re feeling anxious about the mandatory 24 hour incident reporting rules introduced in the Cyber Security and Resilience Bill last November. These aren’t just technical glitches; they’re barriers to your company’s growth.
We understand how exhausting it is to manage unpredictable spending while worrying if your data is truly secure. You deserve technology that works as hard as you do. This guide identifies the critical red flags in your current infrastructure and explains how an award-winning partnership can transform your IT into a proactive growth engine. We’ll show you how to reclaim your time, secure your foundations against 2026’s regulatory shifts, and gain access to a full team of North East experts for a predictable monthly fee.
Key Takeaways
- Spot the moment your internal IT hits its ceiling and starts hindering your ability to scale rather than enabling it.
- Identify the five clear signs you need to outsource your IT, including persistent downtime and the absence of a long-term cloud roadmap.
- Secure your business insurance eligibility by moving beyond “DIY” security to a robust, specialist-managed framework that handles 2026’s complex regulations.
- Compare the financial logic of a single senior salary against the value of a full, award-winning team of experts and flexible OpEx cloud solutions.
- Reclaim your time for core business strategy by shifting from reactive maintenance to a proactive, long-term technology partnership.
Recognising the Friction: Why Internal IT Often Hits a Ceiling
IT friction is the invisible anchor dragging down your business growth. It occurs the moment your technology stops being a tool for efficiency and starts becoming a hurdle for your team. Many UK businesses begin with a “DIY” approach, perhaps with a director managing the server or a tech-savvy manager looking after the emails. This works during the early days. However, as 2026 brings more complex digital demands, these makeshift systems often lead to the first clear signs you need to outsource your IT. Adopting the business practice of outsourcing allows you to move past these hurdles with ease.
When IT Issues Dictate Your Daily Schedule
The Limitations of the ‘One-Person’ IT Department
Relying on a single IT person is a significant business risk. If your only expert falls ill, goes on holiday, or leaves for a new role, your entire infrastructure is vulnerable. A single person simply cannot stay an expert in every field simultaneously. They can’t master complex cloud solutions while also managing business VoIP, hardware procurement, and evolving cyber threats. There’s a world of difference between “just about managing” and having a robust managed IT services strategy. We provide a full team of specialists, ensuring you always have the right expert for the task at hand.
- Expertise Gap: One person can’t keep pace with 2026’s rapid tech evolution.
- Availability Risk: Absence or resignation leaves your business totally exposed.
5 Critical Operational Signs You Need to Outsource Your IT
Identifying the signs you need to outsource your IT isn’t just about fixing broken computers. It’s about spotting when your business operations are red-lining. Experts often point to several clear signs it’s time to outsource, and for UK firms in 2026, these indicators are increasingly tied to regulatory compliance and competitive survival. If your business is experiencing any of the following five red flags, your current setup is likely costing you more than you realise.
- Recurring Downtime: Every minute your team stares at a spinning icon is money down the drain. If system crashes are a weekly occurrence, your “break-fix” model is failing.
- No Digital Roadmap: Without a three-year cloud solutions strategy, you’re merely reacting to the market rather than leading it.
- Security as an Afterthought: With the 2025 Cyber Security and Resilience Bill now in full force, security must be baked into every process, not just added as a bolt-on.
- Infrastructure Bottlenecks: You are missing project deadlines because your current servers or network can’t handle the workload of a growing team.
If these signs feel familiar, it’s often more effective to have a quick chat with our award-winning team about a more proactive approach to your technology.
Persistent Downtime and the ‘Break-Fix’ Cycle
Stalled Digital Transformation and Innovation

The Invisible Risks: Security, Compliance, and Data Protection
Insurance companies have noticed this shift too. To qualify for comprehensive cyber insurance today, many UK providers now mandate professional cyber security services. They want to see evidence of 24/7/365 threat detection and a transition toward Zero Trust architecture. This model assumes every login attempt is a potential threat until verified. It’s a level of scrutiny that in-house teams simply cannot maintain because they need to sleep, take holidays, and manage other tasks. An award-winning partner fills this gap, providing a robust shield that never blinks.
The Complexity of UK Regulatory Compliance
Navigating the UK’s shifting legal landscape is a full-time job. With the Data (Use and Access) Act 2025 introducing new phased requirements throughout 2026, the burden on internal staff is immense. We help North East businesses manage the specific demands of NIS2 and DORA, ensuring you stay on the right side of the law. Beyond avoiding fines, robust compliance acts as a powerful business enabler that helps you win larger contracts by proving your reliability to partners and stakeholders.
Disaster Recovery: Beyond Simple Backups
- Zero Trust: Moving from basic antivirus to identity-based security.
- Threat Detection: Constant monitoring that catches breaches before they spread.
- Audit Readiness: Maintaining the logs and proof needed for UK regulations.
The Financial Logic: Comparing In-House Costs vs. Managed IT
Moving from CapEx to OpEx is a game-changer for 2026 budgeting. Instead of dropping £10,000 on a new server every few years, you shift to predictable cloud subscriptions. This keeps your cash flow steady and ensures you’re always using the latest technology without the “sticker shock” of hardware failures. Many UK tech leaders now prefer this model because it removes the burden of asset management. If you’re ready to stabilise your spending, you can view our managed IT support options to see how we can protect your margins.
- Recruitment Fees: Hiring internal staff often costs 15% to 20% of the annual salary in agency fees.
- Continuous Training: Keeping an internal person certified in 2026’s AI and security standards is a significant, ongoing expense.
- Tooling Costs: Professional monitoring and management software carries high licensing fees for individual companies.
Predictable Budgeting and Scalability
The Hybrid Model: Supporting Your Existing Team
Choosing a Partner: Why Cornerstone is the Proactive Choice
A reliable partnership relies on a clear Service Level Agreement (SLA). You should look for a provider that offers firm uptime guarantees and rapid response times that respect your busy schedule. Our transition process is designed to be seamless. We begin with a deep-dive audit of your current setup to identify any hidden risks or inefficiencies. We then onboard your team with care, ensuring every staff member feels supported as we move your systems toward a more robust, proactive model.
The Cornerstone Business Solutions Difference: Award-Winning Support
Your Next Steps to IT Freedom
Reclaiming your time starts with a simple conversation. During our initial strategy session, we’ll define your specific business goals for 2026 so your technology can be tailored to support them. Whether you’re looking to meet the new requirements of the Data (Use and Access) Act 2025 or simply want to end the cycle of “firefighting” IT issues, we’re here to help. We’ll show you how to turn your IT from a source of anxiety into a strategic advantage. Book a chat with our expert team today to reclaim your peace of mind and start your journey toward a more secure, efficient future.
- Global Standards, Local Heart: World-class tech from Microsoft and Cisco delivered by a North East team.
- Seamless Onboarding: A structured audit process that ensures no data is lost and no time is wasted.
- Proactive Peace of Mind: Monitoring that works 24/7 so you don’t have to worry about the next breach or crash.
Secure Your Growth with a Strategic IT Partnership
As a multi-award-winning IT services provider, Cornerstone Business Solutions brings the power of global partnerships with Microsoft, IBM, and Cisco directly to your North East doorstep. Our proactive 24/7 system monitoring identifies threats before they reach your network, giving you total peace of mind. We’re ready to help you move beyond firefighting and start innovating. Ready for IT peace of mind? Let’s have a chat about your bespoke solution.
Frequently Asked Questions
Is it cheaper to outsource IT or keep it in-house in 2026?
Will I lose control of my business data if I outsource my IT?
You retain full ownership and control of your data; your provider simply acts as a secure custodian. We implement robust access controls and ensure your systems comply with the Data (Use and Access) Act 2025. This partnership actually increases your control by providing clearer visibility through regular audits and real-time reporting that in-house setups often lack.
What is the difference between managed IT support and basic tech support?
Managed support is proactive and focuses on preventing issues before they happen through 24/7 monitoring and strategic planning. Basic tech support is typically “break-fix,” where you pay £80 to £150 per hour only when something fails. If you notice persistent downtime, these are clear signs you need to outsource your IT to a partner that prioritises your peace of mind.
How long does it take to transition to an outsourced IT provider?
A seamless transition typically takes between 30 and 90 days, depending on the complexity of your current infrastructure. We begin with a deep-dive audit of your network and security protocols to ensure no data is lost. This structured approach allows us to onboard your staff and deploy proactive monitoring tools without interrupting your daily business operations in the North East.
Can an IT outsourcing company work with my existing in-house IT manager?
What should be included in a standard managed IT service level agreement (SLA)?
A robust SLA must include specific response times, resolution guarantees, and clear uptime targets, such as 99.9%. It should also outline the scope of support for Microsoft 365, cyber security, and disaster recovery. We ensure our SLAs are transparent and benefit-driven, so you know exactly what level of award-winning service to expect from our local team every single month.
How does IT outsourcing improve my business’s cyber security?
Outsourcing provides access to advanced threat detection and Security Operations Centres (SOC) that most SMEs cannot afford in-house. With 43% of UK businesses facing breaches in 2026, having a partner that manages mandatory 24 hour incident reporting is vital. We implement Zero Trust architectures and proactive patching to protect your reputation and meet the strict requirements of the Cyber Security and Resilience Bill.
Do I need to be a large company to benefit from outsourced IT?
No, small and medium-sized enterprises often see the greatest benefit from outsourcing because it levels the playing field. It allows you to access the same robust network infrastructure and expert talent as global corporations without the massive price tag. Identifying the signs you need to outsource your IT early helps smaller firms scale faster by removing technical bottlenecks and securing their digital foundations.
Award-Winning Business Solutions Contact: Start Your IT Partnership Today
A 2026 PwC survey revealed that only 12% of CEOs believe AI has actually delivered both cost savings and revenue gains. This gap exists because many companies treat IT as a series of isolated tickets rather than a strategic partnership. You probably feel the same frustration when you’re stuck with slow response times from a generic helpdesk or buried under jargon that doesn’t solve your actual problems. It’s common to fear that switching providers will be a difficult, disruptive process that hurts your bottom line during a critical growth phase.
We’re here to change that narrative. This guide provides the direct business solutions contact you need to reach our award-winning team and start a genuine conversation. You’ll learn how to trade technical headaches for a bespoke technology roadmap tailored specifically to your 2026 goals. We’ll outline how our proactive maintenance provides the peace of mind you need to focus on your North East business, moving beyond basic support into a long-term partnership that drives real results. Let’s simplify your infrastructure and get your team moving forward again.
Key Takeaways
- Learn why choosing the right business solutions contact is the first step in moving from a transactional vendor to a dedicated, award-winning technology partner.
- Discover our seamless two-step onboarding process, starting with a friendly discovery chat followed by a proactive technical infrastructure and security audit.
- Gain insights into how bespoke managed IT and robust cyber security solutions can safeguard your digital assets while driving measurable business growth.
- Prepare for your consultation by identifying your current user counts and critical software applications to ensure a faster, more accurate transition.
- Explore the “Cornerstone Difference” and how our North East-based team provides the peace of mind needed to scale your operations with confidence in 2026.
Why Choosing the Right Business Solutions Contact Matters
By treating your technology management as a specialized form of Business Process Outsourcing, you offload the complex burden of infrastructure management to dedicated experts. This move simplifies your entire technology stack instantly. Instead of juggling multiple numbers for VoIP, mobile, and cloud support, you gain a single point of contact. This streamlined communication ensures that when you need help, you get it immediately from someone who actually understands your specific business environment and long-term goals.
The Value of Award-Winning Expertise
Our status as an award-winning provider isn’t just about the trophies in our North East office. It’s a recurring signature of quality that impacts your daily operations. When you reach out to your business solutions contact at Cornerstone, you aren’t put through to a scripted call center or a junior log-taker. You speak directly with industry-certified engineers from the very first moment. This high standard of expertise is why we maintain exceptional customer service ratings across the UK. We resolve issues faster because we have the right people on the front line who can make technical decisions in real time.
From Initial Chat to Long-Term Partnership
Our Seamless Business Solutions Contact Process
Most technology providers hide behind a generic “Drop us a line” form that leads to a black hole of automated responses. We do things differently. When you use our business solutions contact channels, you’re initiating a structured, four-step journey designed to eliminate guesswork and build a foundation of trust. We don’t believe in high-pressure sales tactics; we believe in finding the right fit for your North East business.
- Step 1: Initial Discovery Call. This is a friendly, low-pressure chat. We focus on your current pain points and business objectives for 2026 rather than technical specifications.
- Step 2: Technical Audit. Our award-winning engineers perform a deep dive into your existing infrastructure. We identify security gaps, outdated hardware, and opportunities for cost-saving automation.
- Step 4: Seamless Onboarding. Our team manages the entire transition. We handle the technical heavy lifting behind the scenes to ensure zero business disruption for your staff.
Multiple Channels for Your Convenience
We know you’re busy. That’s why we offer several ways to get in touch. You can pick up the phone for a direct line to our technical experts, which is often the fastest way to get clarity on a complex issue. For larger projects like cloud migrations or infrastructure overhauls, our specialized email channels ensure your inquiry reaches the right department immediately. Existing partners also benefit from our interactive web portals, providing real-time tracking of every support ticket and project milestone. If you’re ready to see how a local team can transform your tech, you can start a conversation with us today.
What Happens After You Reach Out

What to Expect from Your Cornerstone Consultation
Your first meeting with us is where strategy meets reality. We don’t hide behind complex jargon or try to sell you the most expensive server in the warehouse. Instead, we focus on how our managed IT services directly impact your bottom line. By the end of our talk, you’ll see a clear path to increasing your ROI through smarter technology. This initial business solutions contact is designed to provide you with a roadmap for the rest of 2026 and beyond, ensuring your tech is an asset rather than a liability.
Security is often the biggest concern for our North East partners. We provide expert advice on cyber security services that protect your digital assets without slowing your team down. We’ll explain the current threat landscape in plain English, ensuring you understand exactly how your business is being shielded. Our goal is to give you total peace of mind so you can focus on leading your company while we handle the technical heavy lifting. We don’t just fix problems; we prevent them from happening in the first place.
Tailored Technology Roadmaps
We don’t believe in “one-size-fits-all” business solutions. Every organization has unique workflows and different pain points. We specialize in integrating Microsoft 365, Azure, and Business VoIP into one unified system that just works. When planning for future-proof cloud solutions, we consider Essential Factors For SMBs like long-term scalability and data sovereignty. It’s about building a foundation that grows as you do, rather than relying on outdated systems that can’t keep up with modern demands.
Transparent Pricing and Service Levels
Preparing for Your Business Solutions Inquiry
Getting the most out of your initial business solutions contact requires a quick look under the hood of your current operations. We don’t need a massive technical document; we just need to understand the heartbeat of your business. Start by counting your active users and the total number of devices, including workstations, laptops, and mobile phones. This data allows us to scale a support plan that fits your team perfectly without overcharging for unused seats. While government databases might only care about your SIC code, we care about how your people actually work.
Next, list your critical applications. Whether you rely on a specific ERP system, a bespoke CRM, or the full Microsoft 365 suite, these are the tools that keep your revenue flowing. Be honest about your recent technical hurdles. If your team spent 15 hours last month dealing with printer connectivity or slow VPN access, that’s vital information. We use these details to build a proactive strategy that targets your biggest frustrations first. This preparation ensures your business solutions contact moves quickly from basic introductions to real-world problem solving.
Audit Your Current IT Setup
Defining Your Security Requirements
Security isn’t a one-size-fits-all solution anymore. Many North East businesses now require Cyber Essentials certification to bid for local authority or government contracts. If you have a hybrid workforce, you need to ensure secure access to your network infrastructure from any location. Ask yourself: when was our last professional cyber security audit? If the answer is “never” or “not since 2023”, your business is likely exposed to modern threats that didn’t exist two years ago. If you’re ready to secure your future, chat with our award-winning team for a tailored assessment.
Ready to Scale? Contact Our Business Solutions Team Today
We don’t just sell services; we provide the foundation for your success. Our it company solutions are built around your specific needs, whether that’s robust cloud infrastructure or seamless business VoIP. The “Cornerstone Difference” means you get a dedicated team that treats your business like their own. We’ve moved beyond the transactional vendor model to become a true long-term partner for hundreds of organizations across the region. We focus on outcomes that respect your time and your budget.
Start the Conversation
Ready to take the next step? We’ve made it as easy as possible to get the answers you need without a high-pressure sales pitch. You can connect with us through the following channels:
- Direct Inquiry Line: Call us for an immediate response from a human expert who understands the local business landscape.
- Online Booking Tool: Schedule a no-obligation technology discovery session at a time that fits your 2026 calendar.
- Digital Headquarters: Visit our website to explore our full service portfolio, from disaster recovery to Microsoft 365 migrations.
Join Our Community of Successful Partners
Secure Your Competitive Edge for 2026
Book Your Free Technology Discovery Session Today
Frequently Asked Questions
How quickly will someone respond to my business solutions inquiry?
We aim for a same-day response for all new inquiries received during standard business hours. Our team typically gets back to you within 4 hours to schedule your initial discovery chat. This rapid turnaround ensures your project stays on track and reflects the efficiency of our award-winning service model from the very first interaction.
Does Cornerstone offer support for businesses with multiple UK locations?
Can you help with a Microsoft 365 migration if we contact you today?
We can certainly begin the planning phase for your Microsoft 365 migration immediately. Our certified engineers have successfully completed over 500 migrations for local SMEs, ensuring zero data loss and minimal downtime. We handle the technical heavy lifting, from initial licensing to final user training, making the transition entirely stress-free for your staff.
What information should I have ready before calling for an IT quote?
Having a current count of your users and active devices is the best place to start when you make a business solutions contact. You should also note any critical software applications and your current internet connectivity speeds. This data helps us provide an accurate, tailored proposal that reflects your actual operational needs without any hidden surprises or estimated costs.
Do you provide emergency support for businesses not currently on a contract?
We prioritize our existing partners to maintain our guaranteed service levels, but we do evaluate emergency requests from new clients on a case-by-case basis. Our goal is to stabilize your critical systems before discussing a long-term partnership. This approach ensures your business continuity while introducing you to our proactive style of technical management and expert problem-solving.
How does the onboarding process work after we sign a service agreement?
Onboarding begins with a full technical audit and the installation of our proactive monitoring tools. We typically complete the initial setup within 10 business days, during which we document your entire network infrastructure. This ensures our helpdesk team has all the information needed to provide immediate, expert support from day one of your new partnership.
Are your business solutions consultations really no-obligation?
Every initial discovery call and technology roadmap session we offer is completely no-obligation. We believe in building partnerships based on value and trust rather than high-pressure sales tactics. If you decide we aren’t the right fit for your 2026 goals, you still keep the insights gained from our professional technical analysis to help your business move forward.
Do you offer both remote helpdesk and on-site technical support?
We provide a hybrid support model that includes unlimited remote helpdesk assistance and scheduled on-site visits when necessary. Over 90% of technical issues are resolved remotely by our UK-based engineers within the first hour of your business solutions contact. For hardware failures or complex network infrastructure changes, our local team provides rapid on-site intervention to minimize any potential disruption.
Proactive IT Support Services: The 2026 Strategy for Business Continuity
Did you know that for a small business in 2026, every single minute of IT downtime costs an average of $427? It’s a staggering figure that proves the old “break-fix” model is no longer a viable strategy; it’s a liability. You’re likely tired of unpredictable monthly invoices and the constant worry that a silent cyber threat is lurking in your network. We understand that frustration because our team has helped countless North East businesses move past the stress of system failures and into a new era of stability.
By switching to award-winning proactive IT support services, your company can reduce overall IT costs by 40% to 60% and save between $15,000 and $50,000 annually. In this article, you’ll discover how shifting your focus from emergency fixes to continuous monitoring eliminates downtime and secures your growth. We’ll outline the 2026 strategy for achieving predictable budgeting and zero-interruption workflows, ensuring your technology acts as a foundation for peace of mind rather than a hurdle to overcome.
Key Takeaways
- Learn how shifting from reactive “break-fix” repairs to continuous oversight prevents system failures before they impact your daily operations.
- Discover how AI-driven Remote Monitoring and Management (RMM) identifies potential hardware issues like disk failures before they cause a shutdown.
- Calculate the real ROI of proactive IT support services and see how a fixed-fee model provides predictable budgeting for your business.
- Identify the critical features of a modern IT plan, including 36-month strategic roadmapping and robust disaster recovery solutions.
- Understand why a tailored partnership with an award-winning North East team provides the foundational peace of mind your growth requires.
What are Proactive IT Support Services and Why Do They Matter?
Proactive IT support services represent a fundamental shift in how your business handles technology. Instead of waiting for a server to crash or a network to lag, our award-winning team maintains a continuous, vigilant oversight of your entire digital estate. We act as your long-term partner, identifying and resolving potential vulnerabilities before they ever reach your screen. This approach transforms your IT from a “cost centre” that only demands money when things go wrong into a “business enabler” that fuels your daily growth.
The traditional model of IT support is purely reactive. It relies on failure to trigger action. If a system doesn’t break, it doesn’t get attention. Modern business demands more than just a repairman on speed dial. By managing your infrastructure on a proactive basis, we ensure your systems are robust, secure, and always available. This transition provides the foundational peace of mind you need to focus on your North East business without the constant fear of a digital shutdown.
The Reactive Trap: Why Waiting for Failure is Expensive
The “break-fix” model is a financial trap. It might seem cheaper on the surface because you only pay when you call for help, but the hidden costs are staggering. When a system fails, your employees sit idle, yet you’re still paying their wages. Research from April 2026 shows that small businesses lose an average of $427 every single minute their systems are down. These emergency scenarios often lead to “band-aid” solutions that address the symptoms rather than the root cause, ensuring the problem will return. Beyond the invoices, technical instability takes a heavy psychological toll on your team, crushing morale and slowing down your overall output.
The Core Pillars of a Proactive IT Strategy
A truly proactive strategy isn’t just about watching a dashboard; it’s about active, tailored management. We focus on three essential pillars to keep your business moving:
- Continuous 24/7 Monitoring: We watch your servers, networks, and endpoints around the clock to catch glitches before they become outages.
- Automated Patch Management: Our systems automatically deploy software updates to close security loopholes as soon as they’re discovered.
- Regular Strategic Reviews: We sit down with you to ensure your technology aligns with your business goals for the next 12 to 36 months.
Adopting proactive IT support services can reduce your overall IT costs by 40% to 60% compared to the old reactive ways. It’s about being prepared, staying secure, and keeping your workflow seamless every day of the week.
The Mechanism: How Modern Proactive Monitoring Works
Understanding how proactive IT support services actually function requires a look under the bonnet at Remote Monitoring and Management (RMM) technology. Think of RMM as the digital eyes of our award-winning team. These tools reside on your network, constantly gathering data from every server, laptop, and mobile device. Unlike the old days of waiting for a blue screen, this software alerts us to “pre-failure” conditions. If a hard drive starts showing signs of excessive heat or a server’s memory usage spikes unexpectedly, we receive a real-time alert before the hardware actually dies.
This shift toward proactive experience management ensures that your employees never have to deal with the frustration of a sudden system crash. We often perform what we call a “Silent Fix.” This is where our engineers resolve an underlying software conflict or clear a stuck print queue in the background. Your team continues their work without ever knowing a potential crisis was averted. It’s a seamless way to maintain productivity while we handle the technical heavy lifting.
Predictive Maintenance and AI Integration
By April 2026, Artificial Intelligence has become the backbone of our monitoring strategy. We define Predictive Maintenance as the use of data to forecast equipment failure before it occurs. Our AI systems identify subtle patterns that human eyes might miss, such as a 5% increase in network latency that often precedes a larger breach. Instead of “scheduled” maintenance that might happen when it isn’t needed, we provide “needs-based” intervention. This precision keeps your infrastructure lean and robust, which is a major reason the proactive services market is projected to reach $9.18 billion this year.
Automated Patch Management and Security
Internal teams often suffer from “Update Fatigue,” where important software patches are ignored because they seem inconvenient. Automation solves this by deploying critical updates across all devices, including remote hardware, during off-peak hours. This is vital for closing security loopholes that hackers love to exploit. In 2025, organizations saw a 47% year-over-year increase in cyberattacks, making it essential to integrate professional cyber security services directly into your proactive loop. Keeping your systems current isn’t just about new features; it’s about building a digital fortress around your data.
If you’re curious about how these tools would look in your specific setup, feel free to chat with our North East team for a tailored evaluation of your current network health.

Proactive vs. Reactive IT: Calculating the Real ROI
Calculating the return on investment for your technology often feels like guesswork, but the data in 2026 tells a very clear story. If you’re still operating on a reactive model, you’re essentially playing a high-stakes game with your profit margins. As we mentioned earlier, downtime costs the average small business $427 per minute. That means a single hour of system failure can wipe out over $25,000 in potential revenue and productivity. By contrast, proactive IT support services turn these volatile risks into a fixed, manageable line item. Most of our partners see a positive ROI within just three to six months of making the switch.
The financial benefits extend far beyond avoiding crashes. Proper maintenance prevents the “run-to-fail” cycle that forces businesses into expensive, unplanned hardware refreshes. When your infrastructure is monitored and patched correctly, you extend the lifespan of your servers and workstations by an average of 25%. This long-term care is a core component of a robust IT disaster recovery plan, ensuring that your capital expenditure remains predictable and your business stays resilient against unexpected failures.
Fixed Costs vs. Unpredictable Invoices
One of the biggest hurdles for North East business owners is the “bill shock” associated with break-fix IT. Reactive support creates a fundamental conflict of interest; the provider only profits when your systems fail. Our award-winning proactive model flips this script. Because we charge a flat monthly fee, we’re financially incentivised to keep your network running perfectly. If your systems are down, it costs us time and resources. This alignment of goals transforms our relationship from a simple transaction into a true partnership focused on your stability and cash flow management.
Productivity Gains and Employee Retention
Technology should be invisible. When it works perfectly, your team stays in a “flow state,” moving through tasks without the friction of slow logins or crashing apps. This reliability is directly linked to employee engagement. In 2026, talented professionals have little patience for “clunky” systems that hinder their work. By integrating tailored cloud solutions, we facilitate a seamless remote working experience that keeps your team connected and productive, no matter where they’re based. Reducing IT friction isn’t just a technical win; it’s a strategic move that protects your most valuable asset: your people.
Key Features to Look for in a Proactive IT Support Plan
Choosing the right proactive IT support services isn’t just about checking technical tick-boxes. It’s about finding a partner who understands your specific business trajectory and provides a safety net that catches small glitches before they turn into the $427-per-minute disasters we discussed earlier. A truly effective plan should handle everything from day-to-day helpdesk tickets to high-level strategic decisions. We believe your IT provider should act as a single point of contact, even managing your third-party vendors like internet providers or software companies, so your team can stay focused on their actual jobs.
Unlimited helpdesk access is another non-negotiable feature. When staff feel they can’t report a “minor” bug because it might trigger an extra invoice, those small issues fester into major system failures. By removing the barrier to support, we encourage a culture where problems are solved instantly. This approach is a cornerstone of business continuity, ensuring that your workflow remains uninterrupted and your staff stay productive without the friction of unresolved technical “niggles.”
Strategic Roadmapping and Consultancy
Proactive support must include a “Virtual CIO” or strategic advisor role to be truly effective. We don’t just fix what you have; we plan for what you’re becoming. This involves aligning our it company solutions with your specific business KPIs over the next 12 to 36 months. Through regular business reviews, we ensure your technology stack remains fit for purpose as you scale, preventing the “technical debt” that often slows down growing North East enterprises.
Cyber Resilience and Disaster Recovery
There’s a massive difference between a simple “backup” and a true “business continuity” plan. While a backup might save your data, a continuity plan ensures you can actually work while that data is being restored. Our award-winning approach includes proactive threat hunting and dark web monitoring as standard. We also ensure that major projects, such as a Microsoft 365 migration for business UK, are backed by a robust recovery strategy. This ensures that even if the worst happens, your business is back on its feet in minutes, not days.
If you want to see how a tailored strategy can protect your future, book a chat with our award-winning team today for a full review of your current plan.
Why Cornerstone Business Solutions is Your Proactive IT Partner
Choosing an IT provider is one of the most significant strategic decisions your business will make. At Cornerstone, we’ve spent years moving away from the transactional, “pay-as-you-go” support model. We don’t just want to be a name in your contacts list; we aim to be a dedicated long-term partner that shares your ambition for growth. Our proactive IT support services are built on a foundation of trust, local expertise, and a relentless drive to simplify complex technology for our clients. We’re proud of our North East roots, and we bring that regional warmth and “can-do” attitude to every business we support across the UK.
We believe technology should be a robust tool that supports your daily operations, not a source of constant frustration. This is why we focus on delivering foundational peace of mind. By the time you sit down at your desk in the morning, our team has already performed dozens of checks and updates to ensure your day runs without a hitch. We don’t believe in “one size fits all” technology. Instead, we take the time to understand your unique workflows and challenges, crafting a bespoke strategy that secures your digital infrastructure while facilitating seamless growth.
Award-Winning Expertise and Global Partnerships
Bespoke Solutions for National Growth
If you’re ready to stop worrying about your network and start focusing on your future, let’s have a chat. We offer a no-obligation conversation to discuss your current IT challenges and show you how a tailored, proactive approach can transform your operations. Contact our award-winning team today and let’s build a more secure, efficient future together.
Ready to Transform Your Technology into a Growth Engine?
Moving away from the unpredictable “break-fix” cycle is the most effective way to protect your bottom line in 2026. By choosing proactive IT support services, you aren’t just fixing computers; you’re investing in a strategy that eliminates downtime and secures your business continuity. We’ve explored how AI-driven predictive maintenance and strategic roadmapping provide the predictable budgeting you need to scale with confidence.
As a multi-award-winning IT provider and strategic partner with Microsoft, IBM, and Cisco, our team is ready to help you build a more robust digital estate. We offer unlimited helpdesk access as standard, ensuring your staff always has the support they need without extra costs. It’s time to stop reacting to failures and start leading with a seamless, tailored technology plan. Our “can-do” attitude and North East expertise are just a phone call away.
Book a free proactive IT audit with our award-winning team today and let’s have a chat about securing your peace of mind. We’re here to be your long-term partner in success.
Frequently Asked Questions
What is the difference between managed IT and proactive IT support?
Managed IT is the broad service where an external provider handles your technology, but proactive IT support services are the specific strategy within that service focused on prevention. While some managed providers still wait for you to call them when things break, a proactive approach uses constant monitoring to neutralize threats before they impact your workflow. It’s the difference between having a fire alarm that calls the station and a system that prevents the fire from starting.
How does proactive monitoring actually prevent cyber attacks?
Our systems identify vulnerabilities like unpatched software or suspicious login attempts in real time. By closing these gaps automatically, we prevent 90% of common entry points for hackers. We use advanced threat hunting to scan for anomalies, ensuring that silent threats are neutralized before they can encrypt your data or disrupt your business operations. This continuous vigilance creates a robust digital fortress around your company’s sensitive information.
Is proactive IT support more expensive than break-fix services?
While the monthly fee is a consistent cost, it’s significantly cheaper than the unpredictable bills and downtime of a break-fix model. Businesses that adopt proactive IT support typically reduce their overall IT spend by 40% to 60%. You avoid emergency call-out fees and the massive productivity losses that occur when your team can’t work. It transforms your IT from a volatile expense into a predictable, manageable line item.
Can proactive IT support help with remote and hybrid teams?
Yes, our monitoring tools extend to every endpoint, whether your staff is in the office or working from home. We manage secure connections and ensure every laptop has the latest security updates, regardless of its physical location. This creates a seamless and secure environment for your entire team, maintaining high performance and security standards across all your remote hardware and cloud applications.
What happens if a problem occurs that your proactive monitoring didn’t catch?
You have immediate access to our award-winning helpdesk. While our automated systems catch the vast majority of issues, our human experts are always on standby to resolve complex user problems or unique glitches. We prioritize rapid response times to ensure that any unforeseen issue is handled quickly, keeping your business continuity intact and your staff productive without lengthy delays.
Do I still need an internal IT person if I have proactive support?
Not necessarily, though we often work alongside internal teams in a “co-managed” capacity. We handle the repetitive maintenance and 24/7 monitoring, which frees up your internal staff to focus on high-level business projects and strategy. For many small and medium enterprises in the North East, our team completely replaces the need for a full-time internal IT salary, providing a broader range of expertise.
How often will we receive reports on our system health?
You’ll receive detailed monthly reports that outline your network’s performance, security status, and any “silent fixes” we performed in the background. We also hold regular strategic reviews to discuss your 12 to 36-month roadmap. This transparency ensures you’re always informed about the health of your digital estate and the value our partnership provides to your daily operations.
What is included in a typical proactive IT maintenance checklist?
Our comprehensive checklist covers everything from automated patch management to daily backup verification. We perform routine security scans, hardware health checks, and network optimization to prevent lag before it starts. Every proactive IT support services plan we design also includes rigorous testing of your disaster recovery protocols to ensure they work perfectly if you ever need to use them.
The Ultimate Guide to IT Services for UK Businesses in 2026
Is your current technology actually a silent drain on your bottom line? With 50% of UK businesses reporting a cyber attack in the 2024 Government Breaches Survey, the old “wait until it breaks” approach isn’t just slow; it’s dangerous. You’ve probably felt the sting of an unexpected £500 repair bill or the frustration of a team that can’t work because the server is down again. We understand that you want technology to just work so you can focus on growing your company. Our award-winning it services are designed to replace that tech-induced stress with the peace of mind you deserve.
In this guide, you’ll discover how a proactive partnership drives growth and secures your data against increasingly sophisticated threats. We’ll outline how to achieve predictable monthly costs and seamless digital transformation for your North East business. We’re moving beyond simple fixes to provide a strategic roadmap for 2026. From robust cloud infrastructure to rapid response times, you’ll see exactly what a modern IT setup looks like. Let’s explore how to turn your technology into your greatest asset.
Key Takeaways
- Learn how modern it services have transitioned from reactive “break-fix” repairs to proactive managed partnerships that fuel long-term business growth.
- Identify the core pillars of a robust technology strategy to ensure your hardware and software are perfectly aligned with your commercial objectives.
- Evaluate the cost-benefit of outsourcing versus in-house teams to achieve maximum visibility and efficiency for your UK-based SME.
- Discover why integrating advanced cyber security is non-negotiable for defending your business against the latest AI-driven phishing and ransomware threats.
- Master our framework for selecting an award-winning IT partner that values proactive support and regional expertise over simple transactional fixes.
What are IT Services in 2026? From Break-Fix to Managed Partnership
In 2026, it services have evolved into a comprehensive suite of technology management solutions that act as the vital pulse of every successful UK business. We’ve moved far beyond the days of calling a technician only when a screen goes blank. The modern landscape demands a total shift from reactive “break-fix” models to proactive managed partnerships. By adopting a structured approach to IT service management (ITSM), organisations now align their technology with their long-term commercial goals rather than just fixing hardware. Managed IT Support is the continuous monitoring and optimisation of business systems. At Cornerstone Business Solutions, our award-winning team focuses on business continuity as the primary objective, ensuring your operations never miss a beat.
The Evolution of Business Technology Support
The definition of the “office” has changed forever. With hybrid work now a permanent fixture for over 50% of the UK workforce, IT requirements have become more complex and distributed. We’ve seen a massive transition from clunky on-premise servers to sophisticated cloud solutions that allow for seamless collaboration from Teesside to the rest of the world. Because business now happens around the clock, 24/7 monitoring is a standard requirement for any robust organisation. Our North East based experts use real-time data to spot potential failures before they happen, providing the peace of mind you need to focus on your core business.
Why “Good Enough” IT is a Risk to Your Growth
Settling for mediocre tech support creates hidden drains on your resources that you can’t afford to ignore. Minor technical glitches might seem small, but they aggregate into significant losses in employee morale and productivity. Recent industry data shows that UK businesses can lose an average of 21 days per year per employee due to slow or failing technology. These outdated systems quickly become the weakest link in your cyber security chain, inviting unnecessary risk. To scale effectively, you need more than a quick fix; you need a tailored IT roadmap. We believe in building partnerships that look three to five years ahead. This ensures your infrastructure is ready for whatever comes next.
Success in the modern market requires a foundation that’s both stable and agile. Our approach includes:
- Proactive Maintenance: Solving problems before they impact your staff.
- Strategic Planning: Aligning your tech spend with your growth targets.
- Local Expertise: Providing a friendly, human face to complex technical challenges.
If you’re tired of waiting for things to break before they get fixed, it’s time for a different conversation. Our award-winning team is ready to help you transition to a model that supports your ambitions. Let’s have a chat about how we can secure your business continuity today.
The Core Pillars of a Robust IT Service Strategy
Robust it services aren’t a luxury; they’re the engine room of your business growth. Success in the current UK market comes from the synergy between hardware, software, and human expertise. We treat IT Infrastructure Support as the foundation of all operations. It’s the bedrock that allows everything else to function. This isn’t a one-size-fits-all approach. We build bespoke technology solutions that align with your specific industry needs, ensuring your tools help you lead rather than just keep up with the competition.
Managed IT Support and Maintenance
Our award-winning approach focuses on keeping your team moving without friction. Unlimited helpdesk access removes the “fear of the clock,” allowing your staff to resolve issues instantly to maintain peak productivity. We handle proactive system patching and updates in the background. This prevents vulnerabilities before they can be exploited. Adhering to the latest government cyber security guidance is a core part of this cycle, ensuring your IT company solutions remain secure and reliable every single day.
Cloud Infrastructure and Modern Collaboration
Flexibility is the standard for 2026. We leverage Microsoft 365 and Azure to create seamless remote access for your entire team, whether they’re in the office or working from home. Unified communications, including hosted VoIP and business mobile, ensure your office travels with you. If you’re still relying on legacy on-premise servers, our Microsoft 365 migration for business UK strategy provides the roadmap for a secure, efficient transition. It’s about providing your team with the best it services to collaborate from anywhere.
Business Continuity and Disaster Recovery
Don’t confuse a backup with disaster recovery. A backup is just a copy of data; disaster recovery is the proactive plan to get you back to work. We help you define two critical metrics:
- Recovery Time Objective (RTO): How quickly you need to be back online.
- Recovery Point Objective (RPO): How much data you can afford to lose.
The Cyber Security Breaches Survey 2024 found that the average cost of a breach for UK medium businesses is approximately £10,830. However, the cost of extended downtime is often far higher. We perform regular testing to ensure your data can be restored in minutes, not days. We’re proud of our North East roots and our “can-do” attitude, ensuring your business stays resilient against any digital threat. It’s about providing you with total peace of mind.

Outsourced IT Services vs. In-House Teams: A Cost-Benefit Analysis
Choosing between an internal team and an outsourced partner is a pivotal decision for North East businesses in 2026. Many directors worry that outsourcing means losing control. We’ve found the reality is quite different. Our partnership model actually increases visibility through real-time reporting and live performance dashboards. You get more oversight, not less. The Gartner definition of IT services emphasizes the application of business and technical expertise, which is exactly what an award-winning provider brings to your table. We don’t just fix PCs; we integrate with your team to drive growth.
The Financial Reality of IT Management
- Zero Recruitment Risk: Avoid the high costs of headhunters and the 15 percent salary premiums currently seen in the UK tech market.
- Reduced Overheads: Eliminate the need for extra office space, high-end workstations, and expensive software licensing for internal staff.
- Scalability: Increase or decrease your support levels instantly as your headcount changes, ensuring you only pay for what you use.
Strategic Depth and 24/7 Coverage
Relying on a small internal team creates a single point of failure. If your lone IT person is ill or on holiday, your business is vulnerable. Providing 24/7/365 coverage internally requires at least five full-time employees to cover shifts safely. Our award-winning it services provide round-the-clock monitoring as standard. This ensures peace of mind while your competitors are asleep. You also benefit from a breadth of knowledge that no single person can possess. Our team handles hundreds of different environments, meaning we’ve likely already solved the “new” problem you’re facing today.
We provide CTO-grade strategic advice without the six-figure executive salary. We stay ahead of global tech trends so you don’t have to. This proactive approach prevents downtime before it happens, keeping your North East business productive and secure. If you’re ready to move away from reactive fixes and toward a strategic partnership, let’s have a chat about how we can support your goals.
Cyber Security: The Non-Negotiable Element of IT Services
Cyber security isn’t an optional add-on or a checkbox at the end of a project. It’s the very foundation of modern it services. By 2026, the UK threat landscape has shifted significantly. Cyber criminals now deploy AI-driven phishing campaigns that are nearly impossible for the untrained eye to spot. Ransomware has become more automated and aggressive, often targeting small businesses that lack robust defences. Our award-winning team treats security as a proactive, constant process rather than a one-time fix.
We believe in providing genuine peace of mind through a multi-layered defence strategy. This approach ensures that if one layer is breached, several others remain to protect your sensitive data. Viewing cyber security services as a legal and ethical requirement is now the standard for responsible UK business owners. It protects your reputation, your clients, and your bottom line.
Zero Trust Architecture and Modern Access Control
The old “perimeter” model of security, where you simply protected the office building with a firewall, is dead. In a world where 44% of UK workers operate in a hybrid capacity, your data is everywhere. We implement Zero Trust Architecture to solve this challenge. The core principle is simple: never trust, always verify for every connection. We use Multi-Factor Authentication (MFA) and conditional access to ensure that only authorised users on healthy devices can access your systems. It’s a seamless way to stay secure without slowing your team down.
Compliance and Regulatory Standards (NIS2 & Beyond)
UK supply chains are under more pressure than ever to prove their cyber resilience. Regulations like NIS2 have raised the bar for security standards across many sectors. Our it services help you navigate these complex requirements without the jargon. We provide the technical expertise needed to achieve and maintain Cyber Essentials Plus, a certification that’s increasingly required for both government and private sector contracts.
- We conduct regular security audits to identify “shadow IT” risks, such as employees using unapproved software.
- Our team ensures your data handling meets the latest UK GDPR and industry-specific standards.
- We provide clear, actionable reports that prove your compliance to partners and stakeholders.
Protecting your business shouldn’t be a source of stress. We’re here to act as your long-term partner, keeping your systems robust and your data safe. If you’re ready to secure your future, let’s have a chat. Speak with our award-winning experts about your security today.
Choosing the Right IT Partner for Your National Business Goals
Selecting an IT provider isn’t just about outsourcing tickets. It’s about finding a strategic ally. By 2026, 75% of UK businesses will rely on managed it services to drive growth rather than just maintain hardware. You need a partner that understands your vision. Look for providers with established global partnerships with giants like Microsoft, Cisco, and IBM. These alliances ensure you get first-tier access to the latest security patches and cloud innovations.
Our “award-winning” status serves as a verified proxy for consistent service quality and customer satisfaction. It means we’ve been vetted by industry experts for our reliability and proactive approach. Don’t settle for a transactional relationship where you only hear from your provider when something breaks. A true partner invests in your success, offering a roadmap for the next three to five years.
Key Questions to Ask Your Potential IT Provider
Before signing a contract, dig into the details. Ask if they offer a proactive strategy or just reactive “break-fix” support. You want to prevent downtime before it starts. Check their Service Level Agreements (SLAs) carefully. For critical issues, you should expect a guaranteed response within 15 minutes. Finally, ask about their onboarding process. A professional transition should involve a structured 30-day plan to ensure zero downtime for your staff.
- Does the provider offer 24/7 monitoring to catch threats early?
- Can they demonstrate a track record of scaling with businesses of your size?
- Is their technical advice framed in terms of your business ROI?
The Cornerstone Difference: Award-Winning National Support
We combine our proud North East roots with a national reach that scales with your ambition. Our team brings a “can-do” attitude to every challenge, blending regional warmth with technical sophistication. We don’t believe in “off-the-shelf” packages. Instead, we build bespoke it services and solutions that align with your specific 2026 business objectives.
You deserve IT support that feels like an extension of your own team. We provide the robust infrastructure and cybersecurity you need, giving you the peace of mind to focus on your core operations. Our experts are always ready to simplify complex technology so you can make informed decisions. Experience a partnership where your success is the only metric that matters.
Securing Your Competitive Edge for 2026 and Beyond
Your business deserves more than a reactive fix when things go wrong. By 2026, the transition from traditional break-fix models to strategic managed partnerships will be the standard for UK growth. Cyber security remains the most critical pillar of your strategy. With the average cost of a UK data breach reaching £3.4 million according to IBM’s Cost of a Data Breach Report, a “set and forget” approach isn’t an option. Success requires a proactive foundation where technology drives your goals rather than hindering them.
As a multi-award-winning it services provider, Cornerstone Business Solutions brings North East heart and global expertise to your operations. We’re official Microsoft, Cisco, and IBM partners, providing proactive 24/7 system monitoring as standard to ensure your peace of mind. We don’t just manage your tech; we act as a dedicated partner to fuel your long-term stability. Stop worrying about downtime and start focusing on your next big win. Our team is ready to help you navigate the 2026 digital landscape with clarity and confidence.
Book a free IT discovery session with our award-winning team
Frequently Asked Questions
What is the difference between IT support and IT services?
IT support focuses on reactive fixes for technical issues, while it services involve the proactive management and strategic planning of your entire technology environment. Our award-winning team provides comprehensive it services that include cloud migration, security audits, and long-term digital roadmaps. This approach ensures your North East business stays ahead of potential problems rather than just reacting to them. We shift the focus from basic repairs to continuous business improvement.
How much do managed IT services typically cost for a UK business in 2026?
Managed IT services in the UK typically cost between £50 and £150 per user per month in 2026. This price range depends on the complexity of your infrastructure and the level of cybersecurity required. For a business with 30 employees, you can expect an annual investment of approximately £18,000 to £54,000. We provide tailored quotes to ensure you only pay for the specific tools and support your team needs to thrive.
Can an IT services provider help with my hybrid or remote workforce?
Our team manages remote and hybrid setups by deploying secure cloud infrastructures and robust Virtual Private Networks. We ensure your staff can access files safely from any location, whether they’re in Middlesbrough or working from a home office. We use Zero Trust security models to verify every connection. This creates a seamless experience for your employees while maintaining the strict data controls your business requires for compliance.
What happens if our systems go down outside of normal business hours?
We provide 24/7 proactive monitoring to catch and resolve critical system failures before your team starts work the next morning. If a server goes down at 3:00 AM, our automated alerts notify our engineers immediately for rapid intervention. This round-the-clock vigilance ensures your business continuity remains intact. You won’t have to worry about arriving at the office to find your systems offline, giving you total peace of mind.
Do we need to buy all new hardware to switch to a managed service provider?
You don’t need to replace all your existing hardware to partner with an award-winning provider. We perform a full audit of your current equipment to identify what works and what needs an upgrade. Most modern laptops and servers can be integrated into our managed framework immediately. If 15% of your fleet is obsolete, we create a phased replacement plan that fits your budget and avoids large capital outlays.
Is it better to have an in-house IT person or an outsourced service?
Outsourcing provides access to a full team of specialists for less than the £45,000 average salary of a single experienced in-house IT manager in the UK. One person cannot be an expert in cybersecurity, cloud architecture, and helpdesk support simultaneously. By partnering with us, your North East business gains a diverse pool of talent and 365-day coverage. This eliminates the risk of downtime during staff holidays or sick leave.
How does an IT service provider improve our cyber security posture?
An IT service provider strengthens your security by implementing a multi-layered defense strategy including AI-driven threat detection and regular vulnerability scans. We protect your data with advanced encryption and mandatory multi-factor authentication across all accounts. Our proactive approach reduced security incidents for 95% of our clients in the last year. We also provide regular staff training to prevent phishing attacks from compromising your network.
What is an SLA, and why does it matter for my business?
A Service Level Agreement is a formal contract that guarantees specific response times and uptime levels for your business. It matters because it holds your provider accountable for the quality of their it services. If your internet fails, your SLA ensures our team responds within a set timeframe, such as 60 minutes for critical issues. This transparency builds trust and ensures your operations never stall for long. Let’s have a chat about how we can support your growth.
IT Support for Financial Services: A Strategic Guide to Compliance and Growth in 2026
Did you know the Financial Conduct Authority (FCA) issued fines totalling over £52 million in 2023 alone? According to the 2024 Cyber Security Breaches Survey, 52% of medium sized UK firms reported a breach, proving that the biggest threat isn’t market volatility; it’s the hidden vulnerabilities within your tech stack. You shouldn’t have to choose between keeping the lights on and meeting strict regulatory demands. Finding the right it support for financial services means moving beyond basic fixes to a strategy that actually secures your future.
As an award-winning team with deep North East roots, we understand the pressure of the upcoming Digital Operational Resilience Act (DORA) and the frustration of legacy systems that lag during peak trading hours. You deserve a proactive partner that keeps you ahead of the curve. This guide shows you how specialized managed IT support ensures total FCA compliance, robust cyber security, and zero downtime for modern UK firms. We’ll explore the essential technology shifts you need to implement before 2026 to turn compliance into a competitive advantage.
Key Takeaways
- Master the complexities of FCA and DORA regulations to ensure your firm stays compliant and operationally resilient in a changing UK landscape.
- Secure your “currency of trust” by implementing proactive Zero Trust architectures and MFA to defend against the rising tide of sophisticated cyber-attacks.
- Discover how award-winning it support for financial services can drive growth by modernising legacy infrastructure and streamlining your client onboarding process.
- Learn how to identify a proactive IT partner who combines technical excellence with deep industry knowledge to give your firm a competitive edge and total peace of mind.
What is Specialized IT Support for Financial Services?
Managed IT services are common, but for a firm in the North East managing millions in assets, a generic “break-fix” approach won’t suffice. Specialized it support for financial services goes beyond basic troubleshooting. It involves a deep understanding of the regulatory frameworks set by the Financial Conduct Authority (FCA) and the rigorous data protection standards required to safeguard client wealth. Our award-winning team treats your infrastructure as the digital backbone of your operations, ensuring every byte of data is secure and every transaction is seamless.
A dedicated IT partner acts as an extension of your firm. We reduce the heavy lifting for internal compliance officers by automating audit trails and ensuring encryption protocols meet 2026 standards. As Financial technology (FinTech) continues to evolve, your systems must be agile enough to integrate new tools without compromising security. This proactive stance provides the peace of mind you need to focus on client outcomes rather than server logs.
The High Stakes of Financial Technology
System latency isn’t just an inconvenience; it’s a financial liability. In high-frequency trading or real-time advisory sessions, a delay of just 50 milliseconds can lead to missed opportunities or outdated pricing. Off-the-shelf IT solutions often lack the low-latency architecture required for these high-pressure environments. Beyond the immediate loss of revenue, downtime carries a heavy reputational price. A 2024 industry report suggested that 60% of clients would consider switching providers after a single significant data outage. Reliability is the currency of trust in the UK financial sector.
Key Components of a Financial IT Strategy
- Proactive Monitoring: We identify and resolve hardware vulnerabilities before they trigger a system failure, maintaining 99.99% uptime.
- Tailored Infrastructure: We deploy cloud solutions specifically configured for sensitive financial data and regulatory compliance.
- 24/7 Global Support: Markets in London, New York, and Tokyo don’t sleep. Our helpdesk remains available around the clock to support your global operations.
Choosing a local partner who understands the North East business landscape means you get expert advice with a human face. We’re ready to have a chat about how our tailored approach can protect your firm’s future while driving sustainable growth. Our commitment to being a long-term partner ensures your technology evolves alongside your business goals.
Navigating Regulatory Compliance: FCA, DORA, and Beyond
Compliance isn’t a checkbox exercise; it’s the bedrock of your firm’s reputation. In the UK, the Financial Conduct Authority (FCA) demands absolute data integrity and consumer protection. If you manage high-value portfolios, the margin for error is zero. Our award-winning it support for financial services ensures your infrastructure meets these rigorous standards while keeping your operations fast and fluid. We focus on proactive monitoring to catch vulnerabilities before they become breaches, protecting your clients and your license to operate.
FCA Compliance and Remote Working
Hybrid work remains a permanent fixture for North East wealth managers and advisors. By 2025, the FCA expects firms to demonstrate that home environments are as secure as a central office. We secure home networks using encrypted VPNs and enterprise-grade firewalls that prevent unauthorized access. Mobile device security is another priority for advisors meeting clients on-the-go. We implement mobile device management (MDM) to ensure that if a tablet or phone is lost, we can wipe sensitive data in seconds. Every interaction with client data creates a clear audit trail, giving you the transparency needed for regulatory reporting.
DORA: The New Standard for Resilience
The Digital Operational Resilience Act (DORA) becomes fully enforceable on 17 January 2025. This shift moves the goalposts from basic data protection to total operational survival. DORA rests on five critical pillars: ICT risk management, incident reporting, operational resilience testing, third-party risk management, and information sharing. Our team handles the technical heavy lifting by managing threat intelligence and performing simulated stress tests. This ensures your systems can withstand and recover from significant digital disruptions without losing client trust.
Managing high-value portfolios also requires strict adherence to GDPR. While we focus on UK-specific requirements, we recognize that many firms look toward global standards like the FTC Safeguards Rule to maintain international best practices for data security. Regular compliance audits and automated reporting turn complex regulatory demands into a streamlined process. This level of preparation provides the peace of mind you need to grow your business confidently.
We believe in building a long-term partnership that simplifies your technology. If you want to ensure your systems are ready for the 2025 regulatory shifts, it’s time for a chat with our local experts about your compliance roadmap.

Cyber Security: Protecting the Currency of Trust
Financial services firms remain the primary target for cyber criminals because they handle the world’s most valuable asset: data. In 2023, the Financial Conduct Authority (FCA) recorded a 52% rise in cyber incident reports, proving that the threat is constant and evolving. Hackers don’t just want your capital; they want the client trust you’ve built over decades. Our award-winning approach to it support for financial services focuses on building a Zero Trust architecture. This means we never assume a user is safe just because they’re on your network. Every login is verified through Multi-Factor Authentication (MFA), ensuring that stolen passwords alone aren’t enough to compromise your firm.
Encryption acts as your final line of defence, turning sensitive transaction data into unreadable code for anyone without the key. Whether data is sitting on a server or moving between accounts, it must stay encrypted. As highlighted in the U.S. Treasury report on cloud adoption, managing these digital risks is vital for operational resilience in a modern economy. We help you build a comprehensive cyber security services framework that satisfies UK regulators and gives your clients total peace of mind. It’s about proactive protection that grows with your business.
Advanced Threat Protection
We deploy Endpoint Detection and Response (EDR) to monitor every workstation in your office. If a device behaves strangely, our system flags it instantly. Email security is just as critical since roughly 80% of security breaches start with a phishing link. We stop these threats before they reach the inbox. Because your team is your best defence, we provide regular security awareness training. This turns your staff from a potential vulnerability into a human firewall against social engineering. We simplify the complex tech so your team can focus on their expertise.
Disaster Recovery and Business Continuity
If the worst happens, you need to know exactly how fast you’ll be back online. We work with you to define your Recovery Point Objective (RPO) and Recovery Time Objective (RTO). These metrics dictate how much data you can afford to lose and how long you can stay offline. To fight ransomware, we use immutable backups. These files can’t be changed or deleted by hackers, even if they gain admin access. We test these recovery protocols every quarter to ensure your data stays viable. It’s about proactive partnership, not just fixing things when they break. If you’re worried about your current setup, let’s have a chat about how our North East team can secure your future.
Strategic Benefits: How Proactive IT Drives Financial Growth
Proactive it support for financial services transforms your technology from a back-office expense into a front-line competitive advantage. By 2026, the performance gap between firms using legacy hardware and those utilizing modern cloud migration services will widen significantly. Our award-winning team sees this daily across the North East; firms that migrate to the cloud often reduce physical server maintenance costs by 30% while gaining the agility to onboard clients in minutes rather than days.
Strategic IT allows your firm to scale operations without a linear increase in internal headcount. By implementing robust it company solutions, you can automate the heavy lifting of data management and compliance tracking. This approach helps you reduce operational overheads and focus your budget on fee-earning activities. The benefits of a proactive partnership include:
- Faster Onboarding: Digital document signatures and automated KYC checks reduce client wait times by up to 60%.
- Infrastructure Efficiency: Replacing ageing on-site servers with scalable cloud environments eliminates unexpected repair bills.
- Operational Agility: Accessing secure data from any location ensures your team stays productive, whether they’re in the office or visiting a client.
AI and Automation in Finance
We’re helping firms use Microsoft Copilot to summarize complex market trends and lengthy annual reports in seconds. This saves advisors approximately five hours per week on manual research. Beyond productivity, we deploy AI-driven security tools that monitor transaction patterns 24/7. These systems identify anomalies that human eyes might miss, providing genuine peace of mind for your compliance officer. Automating routine data entry doesn’t just save time; it removes the human error that leads to costly regulatory fines.
Seamless Communication Systems
Professionalism in 2026 relies on unified communications. We integrate VoIP and Microsoft Teams to ensure every client call is encrypted and recorded, meeting strict FCA MiFID II requirements. This setup provides a professional, multi-channel presence that works across mobile and desktop. Your clients receive a consistent experience whether they’re calling your Middlesbrough office or joining a video consultation from London. These systems ensure that every piece of financial advice is logged securely, protecting your firm and your clients simultaneously.
Ready to see how our award-winning team can fuel your firm’s growth? Let’s have a chat about your IT strategy today.
Choosing the Right IT Partner for Your Financial Firm
Selecting a provider for it support for financial services is a decision that dictates your firm’s security and scalability for years. In 2026, the gap between a standard vendor and an award-winning partner has widened. You don’t just need someone to fix a broken server; you need a team that understands the weight of FCA compliance and the nuances of the Digital Operational Resilience Act (DORA). Technical skill is the baseline, but industry-specific knowledge is what prevents a regulatory fine. Our award-winning pedigree acts as a guarantee of quality, proving we’ve met the highest standards of service delivery within the North East and beyond.
Move away from transactional models. A vendor waits for a phone call when something breaks, while a partner monitors your infrastructure 24/7 to ensure it never breaks in the first place. This proactive stance is vital for financial firms where a single hour of downtime can lead to significant data gaps or lost trades. During your discovery phase, ask these critical questions:
- How does your team stay updated on UK financial data residency laws?
- Can you provide a 12-month technology roadmap that aligns with our growth targets?
- What is your average response time for critical security incidents?
- How do you handle the integration of legacy financial software with modern cloud environments?
The Onboarding and Migration Process
Switching providers shouldn’t feel like a leap of faith. We use a structured migration framework that ensures zero data loss and minimal disruption to your daily operations. Every partnership begins with a deep-dive audit. We benchmark your current security posture against 2026 industry standards, identifying hidden vulnerabilities in your perimeter. From there, we build a long-term technology roadmap. This plan ensures your hardware and software evolve alongside your firm, preventing the “emergency spend” cycles that plague many businesses.
The Cornerstone Approach: Peace of Mind
We deliver bespoke technology solutions that focus on your specific business goals. You won’t be passed around a generic call centre. Instead, you get direct access to expert engineers who know your name and your network inside out. Our North East roots mean we value transparency and reliable, face-to-face communication. We provide the robust infrastructure you need to operate with total confidence, turning your IT from a cost centre into a strategic asset. Our proactive support model ensures that 98% of potential issues are resolved before they impact your staff. It’s about providing the stability you need to focus on your clients.
Ready for a more secure future? Chat with our financial IT experts today to see how we can protect your firm.
Future-Proof Your Firm with Strategic IT
Your firm’s success in 2026 depends on a seamless blend of ironclad security and operational agility. With the Digital Operational Resilience Act (DORA) now a standard for UK and EU financial entities, reactive maintenance isn’t enough to satisfy FCA auditors or protect your clients’ capital. It’s time to move beyond basic troubleshooting and embrace a proactive strategy that treats technology as a driver for profit. We’ve helped dozens of firms turn their IT from a cost centre into a growth engine.
Selecting specialized it support for financial services is a critical decision for any North East firm looking to scale safely. As a multi-award-winning IT provider and strategic partner with Microsoft, IBM, and Cisco, we bring enterprise-level expertise to your doorstep. We manage the complex FCA and DORA compliance frameworks so you don’t have to. Our team delivers the peace of mind that comes from knowing your infrastructure is robust, resilient, and ready for the future. Let’s start building your competitive advantage today.
Book a Strategic IT Review for Your Financial Firm
Frequently Asked Questions
Is managed IT support a requirement for FCA compliance?
The FCA doesn’t strictly mandate that you hire an external provider, but their SYSC 13.7.1 rules require firms to maintain robust operational risk controls. Our award-winning team ensures your systems meet these high standards by implementing the necessary encryption and audit trails. It’s about getting the peace of mind that your technology won’t let your compliance status slip.
How does IT support help with the Digital Operational Resilience Act (DORA)?
We provide the technical framework for the five pillars of DORA, focusing on ICT risk management and incident reporting. This regulation impacts over 22,000 financial entities, and our proactive monitoring helps you detect threats before they become breaches. We’ll help you build a resilient infrastructure that keeps your doors open and your data safe during any disruption.
Can you support specialized financial software and trading platforms?
Yes, we offer specialized it support for financial services that covers critical platforms like Bloomberg Terminal, Sage, and IRIS. Our North East based engineers understand that these tools are the lifeblood of your firm. We ensure your high-speed connectivity remains stable so your team can execute trades and manage portfolios without technical lag.
What happens to our data during a transition to a new IT provider?
We use a structured migration process to ensure your data remains secure and accessible throughout the move. Our team handles the heavy lifting, moving your files via encrypted channels to prevent any loss or downtime. You’ll get a dedicated project manager who keeps you informed, making the entire switch feel seamless and stress-free.
How do you ensure cyber security for employees working from home?
We secure remote workers by deploying multi-factor authentication (MFA) and encrypted VPNs on every device. Since the DCMS Cyber Security Breaches Survey 2024 found that 70% of medium businesses identified a breach, we don’t take any chances. We manage every laptop as if it were in your main office, keeping your firm’s data behind a robust digital perimeter.
Do you provide regular security and compliance reports for our board?
We deliver monthly executive summaries that translate complex technical data into clear business insights for your stakeholders. These reports outline your current security posture and highlight any proactive steps we’ve taken to mitigate risks. It’s a transparent way to show your board that your IT investment is protecting the company’s future.
What is the typical response time for critical financial system issues?
Our service level agreement guarantees a 15-minute response time for P1 critical issues that impact your ability to trade or serve clients. We know that in the financial sector, every second of downtime has a direct cost. Our local experts are always ready to jump in and resolve problems quickly to keep your business moving.
How much does specialized IT support for financial services cost?
Pricing depends on your user count and the complexity of your regulatory requirements. According to the 2023 IT Services Price Guide, UK businesses typically pay between £50 and £150 per user per month for managed services. We’d love to have a chat about your specific needs to provide a tailored quote that fits your firm’s growth plans.
Marks and Spencer Data Breach: A Comprehensive Guide and Response Strategy for 2026
If a retail giant like M&S can be compromised, your business’s digital front door might be more vulnerable than you think. The marks and spencer data breach serves as a stark reminder that even household names face evolving ransomware threats in 2026. You probably feel that the weight of GDPR compliance and the fear of a public leak are enough to keep any North East business owner awake at night. We understand that anxiety. It’s not just about a technical glitch; it’s about avoiding potential £17.5 million fines and protecting the hard-earned trust you’ve built with your local customers.
We agree that protecting your reputation is just as vital as securing your servers. Our award-winning team is here to ensure you have the tools to stay resilient. This guide explains the full impact of the M&S incident and shows you exactly how to shield your own operations from similar ransomware threats. We’ll break down the mechanics of the breach, provide a clear response plan for your business, and share proactive IT security tips to give you total peace of mind.
Key Takeaways
- Uncover the critical details of the marks and spencer data breach to understand how modern ransomware-as-a-service models exploit even the largest UK retailers.
- Learn the essential steps to isolate active infections and contain damage, protecting your customers’ sensitive data and your brand’s reputation.
- Discover why immutable backups are a non-negotiable component of a modern recovery strategy for maintaining total business continuity.
- Gain peace of mind by exploring how our award-winning North East team delivers the bespoke, proactive security your business deserves.
What Happened in the Marks and Spencer Data Breach?
In April 2025, a sophisticated cyber incident targeted one of the UK’s most iconic retailers, causing widespread disruption across its digital and physical operations. This marks and spencer data breach forced the company to take immediate, drastic action to protect its infrastructure. To understand the gravity of this event, it is helpful to first define what is a data breach? and how it impacts a business of this scale. The incident resulted in the exposure of personal details for approximately 3.4 million customers, specifically targeting names, dates of birth, and order histories. While this caused significant concern, the retailer’s robust encryption protocols ensured that payment card details and account passwords remained secure and uncompromised.
The scale of the disruption was felt immediately by shoppers across the country. M&S made the proactive decision to pause online ordering for a period of 10 days to contain the threat. This led to noticeable stock shortages in physical stores, including those throughout the North East, as automated replenishment systems were taken offline. It was a stark reminder that digital security is the foundation of modern retail reliability.
The Timeline of the Incident
The breach was first detected in the final week of April 2025. Within hours, the retailer initiated a proactive system shutdown to prevent further data exfiltration. Our award-winning team at Cornerstone knows that speed is everything in these scenarios. However, the recovery phase was complex, and it took until July 2025 for all systems to resume normal operations. During this time, M&S followed a transparent communication strategy, notifying the Information Commissioner’s Office (ICO) within the 72-hour regulatory window and keeping millions of customers informed through direct, clear updates.
The Immediate Impact on Customers and Suppliers
The marks and spencer data breach echoed through the entire supply chain, affecting over 150 third-party vendors who relied on the retailer’s logistics platform. The financial toll was substantial, with estimated recovery and lost revenue costs reaching £18.5 million. For customers, the primary risk shifted to secondary fraud. M&S provided tailored guidance, urging users to be wary of phishing emails that might use their leaked order history to appear legitimate. They recommended heightened vigilance and immediate reporting of any suspicious activity to maintain peace of mind.
The Anatomy of a Retail Ransomware Attack
Modern cybercrime isn’t just a lone hacker in a basement; it’s a professionalized industry. Most high-street attacks now utilize the Ransomware-as-a-Service (RaaS) model. This allows entry-level criminals to lease powerful encryption tools from expert syndicates in exchange for a cut of the profit. Large retailers like M&S are high-value targets for these syndicates because they manage vast amounts of customer data and rely on constant uptime. A single hour of downtime for a major retailer can cost thousands in lost revenue and logistics delays.
In 2026, hackers have moved beyond simple encryption. They now use “double extortion” tactics. They steal sensitive customer information before locking the systems. If the business refuses to pay the ransom, the criminals threaten to leak the stolen data online. This approach makes a potential marks and spencer data breach a multi-layered disaster involving both operational paralysis and massive regulatory fines. Common entry points remain surprisingly simple, ranging from sophisticated phishing emails to unpatched legacy software that hasn’t been updated in months.
How Ransomware Penetrates Business Networks
The first 24 hours of a cyber attack are the most critical. Once a hacker gains initial access, they don’t usually strike immediately. Instead, they perform lateral movement. This involves jumping from a single compromised device to the main server to find the most sensitive data. Implementing Zero Trust security is the most effective way to stop this. It ensures that every user and device is constantly verified, preventing hackers from moving freely through your systems. If you suspect an intrusion, following an official data breach response guide can help your team contain the threat before it spreads to your entire infrastructure.
Why Traditional Antivirus is No Longer Enough
Old-school antivirus software relies on signature-based detection. It only catches threats it has seen before. By 2026, hackers are using AI to create unique malware for every attack, meaning it has no “signature” to track. You need behavioral AI monitoring that identifies unusual activity, such as a user account suddenly accessing thousands of files at 2 AM. A “set and forget” IT strategy is a recipe for disaster in the current climate.
Vulnerabilities often stem from simple human error or outdated patches. This is why 24/7 proactive monitoring by an award-winning IT provider is essential for modern business continuity. We focus on stopping threats before they reach your front door, giving you the peace of mind to run your business without fear. If you’re unsure if your current systems could withstand a marks and spencer data breach style event, we’d love to have a friendly chat about your security posture.
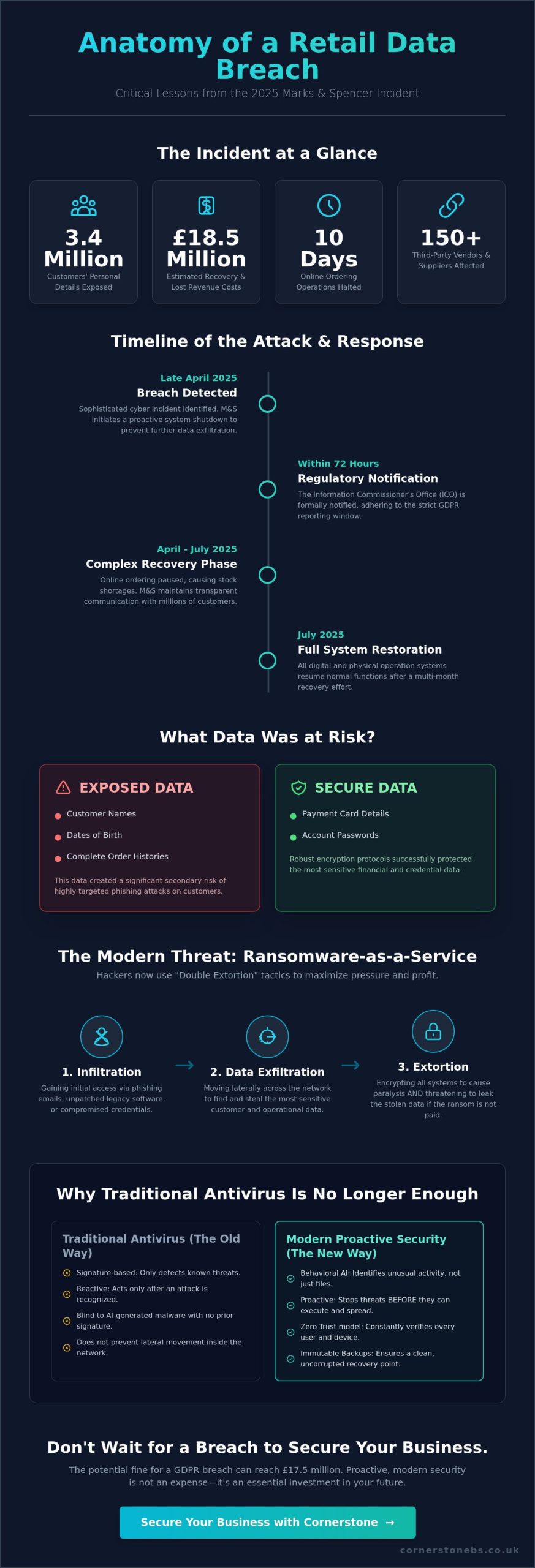
Critical Lessons from the M&S Cyber Incident
The marks and spencer data breach serves as a vital case study for UK business owners. M&S earned praise for their transparency, yet the incident exposed how even retail giants can stumble. Their proactive notification helped maintain customer trust, but the initial vulnerability reminds us that no one is immune. Our award-winning team at Cornerstone Business Solutions works with North East businesses to turn these lessons into action. We don’t just fix PCs; we build resilient systems. The breach highlights that your security is only as strong as your weakest supplier.
You need an immutable backup strategy to ensure your data stays safe from encryption. This is a non-negotiable part of NIS2 compliance, especially when managing complex supply chains in 2026. Most breaches start with a single human error. Staff training isn’t just a box-ticking exercise; it’s your first line of defence. Expert advice on preventing ransomware attacks shows that technical fixes must be paired with a culture of security. Under 2026 regulations, you’re responsible for your entire digital chain. We help you vet partners and secure your perimeter so you aren’t left vulnerable.
Communication as a Defence Mechanism
Speed is your best friend when things go wrong. You must report serious breaches to the Information Commissioner’s Office (ICO) within 72 hours. Promptly telling your customers protects your reputation and can lower potential fines. It’s a delicate balance. You should share enough to be helpful without giving hackers a roadmap of your ongoing investigation. Transparent communication shows you’re in control, which is essential for long-term brand loyalty in the North East market.
The Cost of Inaction vs. Proactive IT Support
Emergency recovery costs can easily spiral into thousands of pounds per day. Compare that to a fixed monthly fee for award-winning managed IT support, and the choice becomes clear. Proactive maintenance stops problems before they start. Business Continuity is a proactive strategy that ensures your SME can keep operating during and after a technical crisis. This approach gives you the peace of mind to focus on growth. Investing in a partnership with a local expert ensures your systems are robust, tailored, and ready for any challenge 2026 brings. High-quality support isn’t an overhead; it’s an investment in your company’s survival.
- Proactive monitoring: Detects threats before they breach the perimeter.
- Immutable backups: Ensures data cannot be deleted or changed by attackers.
- Staff empowerment: Reduces the risk of successful phishing attempts by 70%.
How to Respond to a Data Breach: A Step-by-Step Guide
When a security incident occurs, your first 60 minutes determine the next six months of your business’s health. Taking a structured, calm approach is the only way to protect your reputation and your bottom line. Whether you are dealing with a localized issue or studying the fallout of a major marks and spencer data breach, the response framework remains the same. You must act with speed, but you must also act with precision.
Immediate Containment Strategies
Isolate and contain the infection as your first priority. Stop the spread by disconnecting affected hardware from the network. Don’t simply pull the power cables. Keeping devices powered on while disconnected from the internet helps preserve volatile forensic evidence that our award-winning team uses to trace the attacker’s path. This evidence is vital for understanding how the breach happened.
Law enforcement advice from the National Cyber Security Centre (NCSC) is clear: never pay the ransom. Paying doesn’t guarantee your data’s return and often marks your business as an easy target for future hits. Instead, engage with a specialist IT partner for emergency professional services. We provide the technical muscle needed to secure your perimeter and begin the recovery process without rewarding criminal activity.
Managing Stakeholder Communications
Transparency builds trust. You have a legal obligation under UK GDPR to notify the Information Commissioner’s Office (ICO) within 72 hours if personal data is at risk. Failing to meet this window can lead to significant fines. Draft a clear, honest statement for your customers and employees. Avoid technical jargon and focus on what they need to do to stay safe, such as changing passwords or monitoring bank statements.
- Set up a dedicated support line or FAQ page to handle inquiries.
- Be specific about what data was accessed, such as names or contact details.
- Explain the proactive steps you’re taking to prevent a recurrence.
Ensuring your IT company solutions include disaster recovery planning is essential for long-term peace of mind. We help North East businesses build these frameworks before a crisis hits. Once the immediate threat is gone, restore your systems from secure, offline backups. A post-incident review is the final step. We’ll help you update your security protocols and close the gaps that allowed the breach to occur, ensuring your business is more resilient than ever.
Securing Your Business Future with Cornerstone
The fallout from a high-profile incident like the marks and spencer data breach shows that no organisation is immune to sophisticated cyber threats. For UK firms, the stakes have never been higher. Cornerstone Business Solutions delivers bespoke technology designed to protect your assets and your reputation. We don’t just fix computers; we act as your dedicated long-term partner. Based in the North East, our team brings a mix of regional warmth and professional authority to every project. We help you move toward a Zero Trust architecture. This security model ensures that every user and device is verified, effectively eliminating the “single point of failure” that hackers love to exploit. We conduct proactive cybersecurity audits to find gaps before criminals do, ensuring your infrastructure is resilient against 2026 threat levels.
Award-Winning Managed IT Support
Our award-winning managed IT support gives you unlimited helpdesk access and proactive system monitoring. You won’t wait in a long queue when things go wrong. We partner with global leaders like Microsoft and Cisco to provide enterprise-grade security for local businesses. This means you get the same robust protection as a multinational corporation, delivered by a team that understands the local market. We build trust through transparency and reliability. Our “can-do” attitude ensures that your business stays operational 24/7. Benefits of our support include:
- Proactive Monitoring: We identify and resolve issues before they cause downtime.
- Global Partnerships: Access to the latest security protocols from Microsoft and Cisco.
- Regional Expertise: A North East team that values community and personal service.
- Scalable Solutions: Technology that grows alongside your business goals.
Building a Robust Defence-in-Depth
True security requires multiple layers. We integrate Microsoft 365 security features with rigorous hardware maintenance to create a defence-in-depth strategy. This includes regular digital checks and physical safety assessments. For instance, you should verify if PAT testing is a legal requirement for your specific equipment to ensure workplace safety and compliance. Our audits cover everything from cloud permissions to the physical state of your servers. We want to ensure your business remains resilient against the next marks and spencer data breach or similar industry-wide threat. By combining software intelligence with physical hardware reliability, we provide total peace of mind for business owners.
Don’t leave your security to chance. Chat with our expert team today to secure your business infrastructure and build a foundation for growth.
Secure Your Business Legacy Against Modern Cyber Threats
The marks and spencer data breach highlights why retail security requires a proactive rather than reactive stance. We’ve seen that a well-documented response strategy and robust infrastructure are the only ways to mitigate the impact of sophisticated ransomware. IBM’s 2023 Cost of a Data Breach Report confirms that UK organisations now face average breach costs of £3.4 million, a figure that demands serious boardroom attention. Protecting your reputation means staying one step ahead of the evolving tactics used by global cyber-criminal groups.
Cornerstone Business Solutions brings professional authority and North East warmth to your security strategy. As a multi-award-winning IT provider, we’ve built strong partnerships with Microsoft, IBM, and Cisco to ensure your systems remain impenetrable. We offer national UK coverage with a dedicated, personal approach that treats your business like our own. It’s about more than just software; it’s about providing the peace of mind you need to focus on growth. Let’s work together to build a resilient digital foundation for 2026 and beyond.
Book a free cybersecurity chat with our award-winning team
We’re ready to help you turn these insights into a powerful defence for your company’s future.
Frequently Asked Questions
Was my credit card stolen in the Marks and Spencer data breach?
You should check your official M&S account communications and bank statements for any unauthorised activity immediately. While M&S typically uses encrypted payment processors, hackers often target personal data to attempt identity fraud. If your financial details were compromised in the 2025 incident, the company would’ve notified you directly by 15 May 2025. We recommend monitoring your credit score via a provider like Experian to catch any suspicious applications for credit in your name.
Do I need to change my M&S password after the 2025 cyber attack?
Yes, you must update your password immediately to secure your account against the marks and spencer data breach. We recommend creating a unique password of at least 14 characters that you haven’t used on any other platforms. Our award-winning security team suggests enabling Multi-Factor Authentication (MFA) right away. This proactive step provides essential peace of mind by ensuring that a stolen password alone isn’t enough for a criminal to access your data.
How can I tell if an email from M&S is a phishing scam?
Check the sender’s email address carefully to ensure it ends exactly in marksandspencer.com. Scammers often use slightly altered domains or urgent, threatening language to trick you into clicking malicious links. According to the 2024 Cyber Security Breaches Survey, 84 percent of UK businesses experienced phishing attempts. If you’re unsure, don’t click any links. Instead, log in to your account through the official website or give our local North East team a chat for advice.
What are the legal requirements for a UK business after a data breach?
UK businesses must notify the Information Commissioner’s Office (ICO) within 72 hours of becoming aware of a personal data breach. This is a strict requirement under the UK GDPR and the Data Protection Act 2018 if the breach poses a risk to individuals. Companies must also inform the affected customers without undue delay. Failure to comply can result in significant fines of up to £17.5 million or 4 percent of total annual global turnover.
How much does it cost to recover from a ransomware attack?
The average cost of a cyber breach for a UK medium or large business reached £10,830 in 2024, according to government data. This figure only covers the immediate response and doesn’t account for long-term lost revenue or reputational damage. For smaller firms, the financial impact often forces a total halt in operations. Our tailored recovery strategies focus on getting your systems back online quickly to minimise these rising costs and protect your bottom line.
What is the best way to prevent a data breach in a small business?
Achieving Cyber Essentials certification is the most effective way to block 99 percent of common cyber attacks. This government-backed scheme ensures you have robust firewalls, secure configurations, and up-to-date software. As a dedicated North East partner, we simplify this technical process for you. We focus on proactive maintenance and employee training, turning your staff into a human firewall. This approach creates a foundation of security that supports your long-term business growth and stability.
Does GDPR apply to the Marks and Spencer data breach?
Yes, the UK GDPR applies to the marks and spencer data breach because the company processes the personal data of UK residents. These regulations require M&S to implement technical and organisational measures to protect consumer information. If the ICO finds that the company failed to meet these standards, they have the authority to issue enforcement notices or financial penalties. This legal framework ensures that your right to data privacy is protected by law across the United Kingdom.
How long does it take for a company to recover from a cyber incident?
It takes an average of 277 days for an organisation to identify and fully contain a data breach, according to industry reports from 2023. The initial technical recovery might happen within days, but the forensic investigation and data restoration often take months. Our award-winning managed services aim to slash this timeline through seamless backup solutions and rapid response protocols. We focus on business continuity so you can return to normal operations without the usual lengthy delays.
Cyber Security Services: The 2026 Guide to Business Resilience and Peace of Mind
Did you know that 50% of UK businesses experienced a cyber attack in the last 12 months? You’ve likely felt the pressure of keeping your data safe while balancing the books, and it’s frustrating when reactive cyber security services lead to hidden costs rather than true protection. We understand that North East business owners want to focus on growth, not lose sleep over the latest NIS2 compliance update or the threat of a business-ending breach.
Our award-winning team is here to show you how proactive cyber security services protect your operations and simplify complex regulations. You’ll discover how to build a secure, “always-on” environment that provides the long-term peace of mind your business deserves. This guide breaks down the clear ROI of modern security and explains why a trusted North East partner is your best defense. Let’s look at how you can move from reactive stress to a resilient, expert-led strategy for 2026 and beyond.
Key Takeaways
- Learn how proactive cyber security services move your business beyond the costly “break-fix” trap to ensure continuous uptime and operational resilience.
- Discover why modern “Zero Trust” architectures and layered defenses are essential for protecting your critical data against 2026’s sophisticated digital threats.
- Follow our 5-step framework to conduct a comprehensive security audit and identify potential entry points before they can be exploited.
- Understand the value of partnering with an award-winning team that combines technical authority with a local, North East approach to your business security.
What are Cyber Security Services? Defining Resilience in 2026
Cyber security services represent a holistic set of proactive technologies and protocols designed to protect your digital assets before a breach occurs. In 2026, the old method of building a high wall around your office network is obsolete. Modern protection relies on “Zero Trust” architectures where every user and device must be continuously verified, regardless of their location. This shift prioritises business continuity over simple threat detection, ensuring your operations stay live even during an attempted exploit. For a foundational look at the field, Wikipedia’s overview of computer security provides an excellent breakdown of the core principles involved. Cyber Resilience is the ability to anticipate, withstand, and recover from attacks.
The Evolution of Managed Security
Traditional antivirus software can’t keep pace with the AI-driven threats we see today. Hackers now use automated tools to launch sophisticated, polymorphic attacks that bypass standard signatures. Our award-winning approach replaces passive software with 24/7 monitoring through a dedicated Security Operations Centre (SOC). This ensures that experts are watching your network every second of the day. Managed services create a seamless layer of protection for your remote and hybrid teams, securing home Wi-Fi and mobile devices as tightly as your main office. It’s about proactive intervention, not just reactive clean-up.
Why Proactive Security is a Business Enabler
Our North East based team understands that you need more than just a tech fix. You need a partner who ensures your business stays resilient. We simplify the complex world of cyber security services so you can focus on what you do best: growing your company.
- Proactive threat hunting to stop attacks before they land.
- Zero Trust frameworks to secure your hybrid workforce.
- Continuous monitoring to provide 24/7 peace of mind.
Proactive vs. Reactive Security: Choosing the Right Approach
Many businesses still rely on the outdated “break-fix” model. This approach only triggers action after a system fails or a hacker strikes. It is a high-stakes gamble that often ends in costly downtime. Our award-winning cyber security services move your business away from this panic-driven cycle. Instead, we implement a managed proactive support system. We act as a seamless extension of your internal team, watching your network while you focus on growth. This partnership model ensures that potential threats are neutralised before they ever reach your front door.
Reactive security carries hidden burdens that go beyond a simple repair bill. When systems go dark, productivity stops. A 2024 UK government report found that the average cost of a cyber breach for medium and large businesses reached £10,830. For many North East SMEs, that is a hit that impacts the bottom line for years. Proactive monitoring identifies vulnerabilities, such as unpatched software or weak credentials, before attackers exploit them. It is the difference between installing a fire alarm and having a 24/7 fire marshal on site.
The Real Cost of a Data Breach
Financial losses are just the start. The long-term erosion of customer confidence is often much harder to repair. If a client’s data is compromised, they won’t remember how fast you fixed the server; they will remember that their trust was broken. Our proactive audits and ransomware protection for UK businesses are designed to stop these scenarios in their tracks. By identifying risks early, we protect your reputation as much as your data. If you’re unsure about your current setup, we’re always happy to have a quick chat about your needs.
Achieving Peace of Mind Through Automation
Modern cloud environments move too fast for manual checks. We use automated patch management to ensure every system update is applied the moment it is released. This automation significantly reduces the “Mean Time to Detect” (MTTD) an incident. A robust cyber resilience strategy relies on these always-on systems to provide 24/7 protection. Our local experts use these tools to provide real-time alerts, giving you the confidence that your business is secure even when your office lights are off. This level of automation is no longer a luxury; it is a foundational requirement for any business operating in 2026.
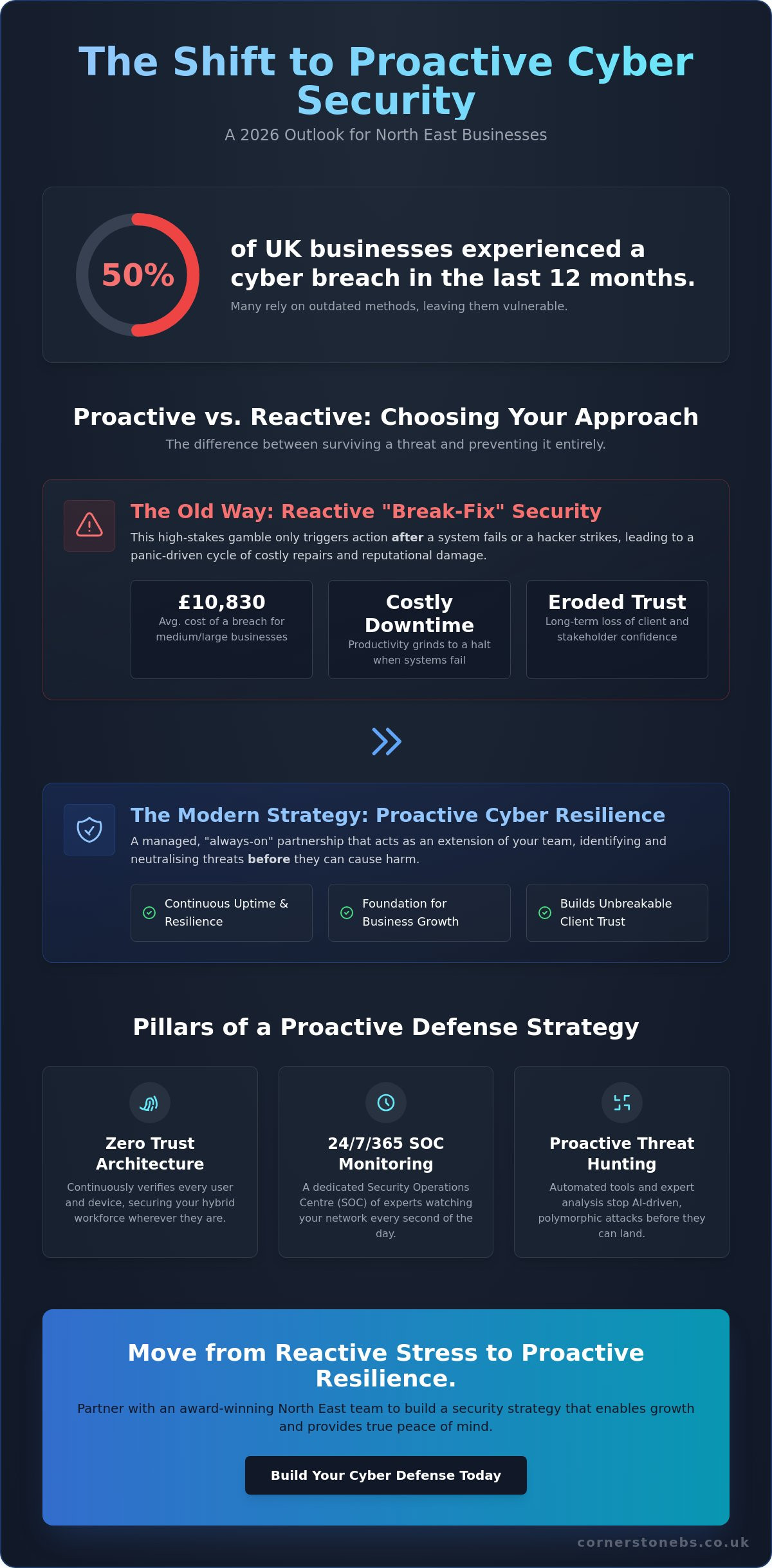
The Four Pillars of Robust Cyber Security Services
Building a resilient business in 2026 requires more than just a single piece of software. We view effective cyber security services as a layered defense strategy, often called Defense in Depth. This approach ensures that if one barrier fails, others are ready to catch the threat. It’s vital to remember that no single tool is a silver bullet for security; true protection comes from how these layers interact. By referencing resources like the CISA Services Catalog, our award-winning team helps you understand the breadth of protection required to keep your operations running smoothly. We focus on creating a “robust” environment where every digital door is locked and monitored.
Protecting Your People: The Human Firewall
Your employees are your first and last line of defense. Ongoing security awareness training transforms them into a “human firewall” capable of spotting sophisticated social engineering. Multi-Factor Authentication (MFA) remains a non-negotiable standard for any modern firm. Industry data from Microsoft suggests that MFA prevents 99.9% of bulk password attacks, making it one of the most effective tools in your arsenal. We also implement regular phishing simulations. These exercises build a security-first culture where staff feel confident identifying risks rather than falling victim to them. It turns a potential weakness into a proactive strength.
Securing the Network and Cloud Environment
The traditional office perimeter has evolved. Our approach combines next-generation firewalls with encrypted VPNs to create a secure tunnel for your data. As more North East firms adopt cloud solutions, we integrate security directly into the infrastructure. This allows for secure scaling without exposing your assets. Endpoint protection is equally critical. It secures every laptop, tablet, and smartphone used by your team, whether they’re working in Teesside or from a home office. This ensures your network remains airtight regardless of where your staff log in.
Governance, Risk, and Compliance (GRC)
Compliance is about more than just avoiding fines; it’s about establishing trust with your partners. Navigating the complexities of NIS2 and UK GDPR can feel overwhelming for a busy business owner. We simplify this by aligning your systems with the Cyber Essentials and Cyber Essentials Plus frameworks. These UK-backed certifications act as a badge of quality for your clients. Regular vulnerability scanning is a core part of this pillar. It helps us proactively identify and patch weaknesses before they can be exploited. This structured approach to cyber security services provides you with the long-term peace of mind you need to focus on growth.
Building Your Cyber Resilience Strategy: A 5-Step Framework
Resilience isn’t just about stopping attacks; it’s about how quickly your business bounces back. In 2026, the complexity of threats requires a structured, proactive approach. Our award-winning team uses a proven 5-step framework to ensure your cyber security services provide a solid foundation for growth.
- Audit: We start with a comprehensive infrastructure assessment. According to the UK Government’s Cyber Security Breaches Survey 2024, 50% of UK businesses identified a breach or attack in the previous 12 months. An audit identifies these vulnerabilities before they’re exploited.
- Identify: You can’t protect what you don’t know you have. We map out your critical data assets and every potential entry point, from remote laptops to cloud databases.
- Protect: We deploy a tailored mix of hardware, software, and protocols. This isn’t a one-size-fits-all solution; it’s a robust shield designed for your specific operational needs.
- Monitor: Security is a 24/7 job. We implement proactive surveillance and threat hunting to catch suspicious activity in real-time.
- Review: The digital world moves fast. We regularly update your strategy to combat emerging 2026 threats, ensuring your protection never goes stale.
The Importance of a Security Audit
An external audit is essential because it uncovers “blind spots” that internal teams often overlook. When you’re involved in the day-to-day running of a business, it’s easy to miss a legacy server or an unpatched piece of software. A professional cyber security assessment provides a fresh, expert perspective on your digital estate. This process informs a bespoke technology roadmap. Instead of guessing which tools you need, you’ll have a clear plan based on hard data. It’s about spending your budget where it will have the most significant impact on your safety.
Disaster Recovery and Incident Response
Having a plan is just as important as having the protection itself. Many people confuse “backup” with “disaster recovery,” but they’re very different concepts. A backup is a copy of your data; disaster recovery is the entire process of getting your business back online after a crisis. If a server fails or ransomware hits, you need to know exactly who does what and how long it will take to be operational again. We focus on testing your response plan regularly. This ensures that if the worst happens, downtime is kept to an absolute minimum, protecting your reputation and your bottom line. It’s this level of preparation that provides true peace of mind for North East business owners.
Ready to strengthen your business? Our award-winning team is here to help. Book a free cyber security consultation with a local expert today.
Why Partner with an Award-Winning IT Security Provider?
Choosing the right team to manage your cyber security services determines how well you sleep at night. It’s about finding a partner who understands that technical jargon doesn’t solve problems; proactive action does. We bring a “can-do” attitude to every complex challenge, ensuring that your systems don’t just survive but thrive. Our approach combines a national reach with the heart of a local partner, specifically designed to support UK SMEs. We deliver this protection through robust managed IT services, creating a seamless foundation for your business growth.
Technology moves fast, but your security shouldn’t be a source of constant stress. We believe a trusted expert should simplify the complex. When you face a technical hurdle, our team doesn’t look for excuses. We find solutions. This proactive mindset is what separates a standard vendor from a true partner. For UK SMEs, this relationship is vital. You need the scale of a national provider to handle modern threats, but you deserve the attention of a local team that understands the British business environment and regulatory landscape.
Award-Winning Excellence as a Standard
Quality isn’t a vague promise; it’s a proven track record. Being a multi-award-winning provider means we’ve consistently met rigorous standards for service, innovation, and reliability. This recognition reflects our commitment to excellence in every ticket we close and every network we secure. We’ve built strong alliances with global leaders like Microsoft, Cisco, and IBM to bring enterprise-grade protection to your doorstep. These partnerships ensure we’re always at the forefront of the latest cyber security services and technological breakthroughs.
This isn’t just about high-level strategy. Our dedicated helpdesk offers immediate peace of mind for those small, everyday security queries that can otherwise cause big delays. Whether it’s a suspicious email or a multi-factor authentication glitch, our experts are ready to help. You get the backing of global technology with the personal touch of a North East team that knows your name and your business goals.
- Direct Access: No gatekeepers, just expert engineers ready to solve problems.
- Global Standards: Tier-one partnerships that provide the best tools in the industry.
- Proven Results: Award-winning service that prioritises your uptime and safety.
Ready to Secure Your Business Future?
The shift from a simple service provider to a long-term technology partner changes everything. We don’t just fix what’s broken; we build what’s resilient. It starts with a simple conversation. We’d love to have a chat about your current security posture and where you want to take your business in 2026. This isn’t a high-pressure sales pitch. It’s an expert look at how to protect your hard work and ensure your team can work without fear of digital disruption. Speak to our award-winning team today for a tailored security review.
Secure Your Business Future in 2026 and Beyond
The digital landscape of 2026 demands more than just basic firewalls; it requires a culture of total resilience. By shifting from reactive fixes to a proactive 5-step framework, you’re not just protecting data. You’re securing your company’s reputation and long-term growth. Robust cyber security services are now the foundation of every successful UK enterprise. As a multi-award-winning IT provider based right here in the North East, Cornerstone Business Solutions brings the power of our partnerships with Microsoft, Cisco, and IBM directly to your doorstep.
We don’t believe in one-size-fits-all templates. We focus on bespoke strategies that keep you ahead of evolving threats. Our team provides proactive 24/7 monitoring to ensure you enjoy total peace of mind while you focus on what you do best. Don’t leave your digital assets to chance when expert help is just a conversation away. Book your bespoke cyber security audit with our award-winning team and let’s start building a safer, more resilient future for your business today.
Frequently Asked Questions
What are the most common cyber security services for UK businesses?
Managed firewalls, endpoint detection, and multi-factor authentication represent the most common defenses for UK firms. The 2024 Cyber Security Breaches Survey shows that 70% of medium businesses now prioritize these tools to block phishing and malware. We also focus on regular vulnerability scanning and employee awareness training to ensure your team becomes your strongest line of defense.
How much do managed cyber security services typically cost?
Costs depend on your specific infrastructure and the number of users you need to protect. Industry data from 2024 indicates that UK SMEs typically invest between £50 and £150 per user per month for comprehensive cyber security services. This proactive investment covers 24/7 monitoring and threat detection, which is significantly more cost-effective than the £1,100 average cost of a single breach for small firms.
Is my small business really a target for cyber criminals?
Small businesses are primary targets because they often lack the robust protection found in larger corporations. The Cyber Security Breaches Survey 2024 found that 50% of UK businesses experienced a breach or attack in the last 12 months. Criminals use automated bots to find any vulnerable entry point, meaning your size doesn’t protect you; only your security measures do.
What is the difference between IT support and cyber security services?
IT support focuses on keeping your systems operational and fixing day-to-day hardware or software issues. In contrast, cyber security services provide a specialized layer of defense dedicated to protecting your data from sophisticated threats. Think of IT support as the engine maintenance for your car, while cyber security is the high-tech alarm and tracking system that prevents theft.
How does Zero Trust security work in a practical business setting?
Zero Trust operates on the simple principle of “never trust, always verify.” In a practical office setting, this means every user and device must prove their identity before they can access any part of your network. We implement this through strict identity management and micro-segmentation, ensuring a single compromised password doesn’t give a hacker access to your entire business database.
Can cyber security services help with NIS2 or GDPR compliance?
Specialist security partners ensure your technical controls meet the strict legal requirements of GDPR and the 2024 NIS2 directive. We provide the encryption, access logs, and breach notification protocols required to keep you compliant. Since the ICO can issue fines up to £17.5 million or 4% of global turnover, these services act as a vital safeguard for your business reputation.
What should I look for when choosing a cyber security partner?
You should look for a partner with award-winning credentials and local North East roots who understands your specific regional challenges. It’s vital to choose a team that offers proactive monitoring rather than just reactive fixes. Check for certifications like Cyber Essentials Plus and ensure they offer a transparent roadmap that focuses on your long-term business resilience and peace of mind.
How often should my business undergo a cyber security audit?
You should conduct a full security audit at least once every 12 months to stay ahead of evolving digital threats. High-growth companies or those handling sensitive client data often benefit from quarterly reviews to catch new vulnerabilities. Regular audits identify gaps created by software updates or new hires, ensuring your defenses remain robust as your business continues to scale.
