Could a piece of EU legislation actually be the most important security upgrade your North East business makes in 2026? You likely feel that nis2 compliance is just another complex hurdle to clear, especially when you’re already busy managing local UK operations. It’s completely normal to feel frustrated by technical jargon or the threat of non-compliance penalties that can reach upwards of £8.4 million for essential service providers under Article 34 of the directive.
We’ve designed this guide to replace that confusion with a clear, proactive roadmap. As an award-winning IT partner, we want to simplify these requirements so you can focus on your core business while we ensure your digital supply chain is robust and resilient. We’ll walk you through a definitive “yes or no” scope check, a prioritised list of security improvements, and a plan to achieve total peace of mind. Let’s take the stress out of your digital protection together.
Key Takeaways
- Understand why the NIS2 Directive applies to UK businesses trading with the EU and how it impacts your digital supply chain.
- Discover how to categorise your organisation as “Essential” or “Important” based on the new size-cap rules and specific industry sectors.
- Learn the 10 essential security pillars required for nis2 compliance to build a robust and resilient cyber security framework.
- Gain actionable insights on implementing a risk management strategy that fosters a proactive, “security-first” culture from the boardroom down.
- See why partnering with an award-winning North East expert can simplify complex technical requirements and deliver total peace of mind.
Understanding NIS2 Compliance for UK Organisations
The NIS2 Directive, which came into force in January 2023, serves as the successor to the original 2016 NIS regulations. It represents a significant step forward in Cyber-security regulation, designed to harmonise and strengthen resilience across the European Union. At Cornerstone Business Solutions, our award-winning team specialises in interpreting these complex frameworks for local firms. We believe that nis2 compliance is more than just a box-ticking exercise; it’s a commitment to robust business continuity.
Why Does an EU Directive Matter in the UK?
You might wonder why an EU law impacts a business based in Teesside or Tyneside. The answer lies in the principle of extra-territoriality. If your organisation provides services into the EU or operates as a critical supplier for European essential services, you fall directly under its scope. Industry data indicates that roughly 15% of UK businesses currently trade with EU partners, making this a widespread concern. If you can’t demonstrate nis2 compliance, you risk being “de-selected” during the procurement process. European firms are increasingly auditing their British suppliers to ensure their own compliance isn’t compromised by a weak link in the chain.
The Consequences of Non-Compliance
The financial stakes are high for those who ignore these updates. Non-compliant organisations face fines of up to £8.5 million or 2% of their total global annual turnover, whichever is higher. It’s a heavy price for any business to pay. Perhaps more importantly, the directive introduces personal liability for management bodies. This means C-suite executives and directors can be held personally responsible for cybersecurity failures. We focus on providing the “peace of mind” that comes from knowing your leadership is protected. Beyond the threat of fines, the loss of reputation following a breach can be devastating, as demonstrated by the Marks and Spencer data breach which showed how even household names face severe reputational and financial consequences from ransomware attacks. We act as your long-term partner to ensure your business remains both secure and reputable in a competitive market.
Determining Your Entity Status: Are You Essential or Important?
Identifying your organisation’s classification is the foundation of a solid nis2 compliance strategy. The directive doesn’t apply to everyone, but its reach is far wider than previous regulations. It primarily targets medium and large enterprises. If your business employs more than 50 people or has an annual turnover exceeding £8.6 million, you must determine which of the two categories you fall into. This ensures our local North East supply chains remain robust against evolving threats.
The distinction between “Essential” and “Important” depends on the criticality of your sector. While the 2024 UK Cyber Security and Resilience Bill will refine these definitions for the British market, they closely mirror the 18 sectors identified by the EU. Regardless of your label, the underlying security requirements are equally stringent. You’ll need to implement proactive measures to protect your operations and your clients’ data. If you’re feeling overwhelmed by the technical jargon, our award-winning team is always ready for a friendly chat to simplify your path to protection.
Essential Entities: High-Stakes Sectors
- Proactive Supervision: Regulators don’t wait for a breach. They’ll conduct regular audits to ensure you’re meeting standards.
- Strict Reporting: You’re under a microscope regarding incident reporting timelines, with 24-hour early warnings often required.
- High Scrutiny: Expect frequent, detailed checks on your risk management frameworks and supply chain security.
Important Entities: The Broader Net
The “Important” category captures seven other critical sectors that are vital but slightly less sensitive than those in the Essential group. This includes food production and distribution, postal services, waste management, and chemical manufacturing. Digital providers, such as online marketplaces and search engines, also fall under this banner. It’s a broad net designed to catch the wider supply chain that keeps the UK running.
The main difference lies in the supervision model. Important entities are subject to reactive supervision. This means authorities typically only step in if they receive evidence of non-compliance or after a security incident has occurred. Don’t let this lighter oversight fool you. The actual security obligations and nis2 compliance standards are identical to those for Essential entities. You must still implement robust encryption, multi-factor authentication, and incident response plans. Failing to do so can result in the same heavy fines, which can reach up to £6 million or 1.4% of global turnover for Important entities.
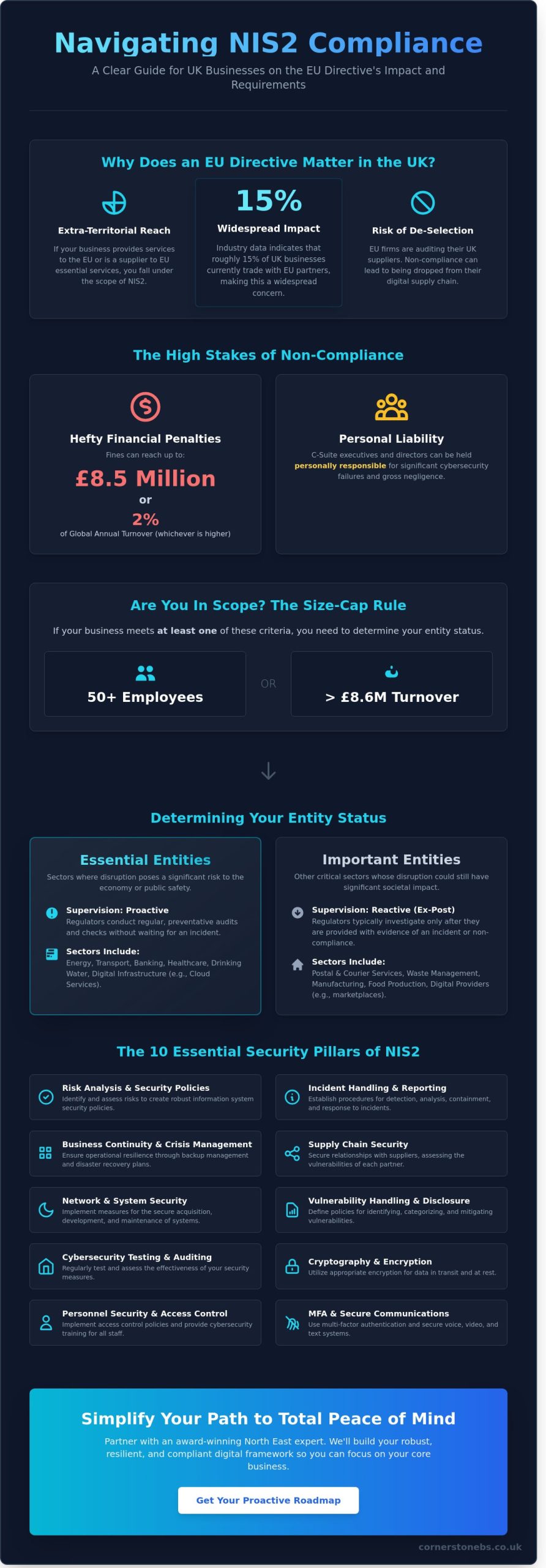
The 10 Pillars of NIS2 Compliance: Your Practical Checklist
Article 21 of the directive outlines ten specific security measures that form the bedrock of your nis2 compliance journey. These aren’t just bureaucratic hurdles. They represent a foundational cyber security strategy designed to keep your operations running smoothly. The UK government is currently aligning our national standards with these principles through the Cyber Security and Resilience Bill, making these steps essential for any forward-thinking North East business.
Your security measures must be proportionate. This means the complexity of your defence should match your firm’s size and the specific risks you face. A local manufacturer won’t need the same setup as a global financial hub, but both must prove they’ve taken appropriate action. Documenting every step is vital. If an audit occurs in 2026, your records will provide the peace of mind that you’ve met your legal obligations.
Risk Management and Information System Security
Effective security starts with knowing your weaknesses. You need established protocols for regular vulnerability scanning and comprehensive risk assessments. These shouldn’t be annual events; they’re ongoing processes. You’ll also need clear policies on cryptography and encryption to protect sensitive data at rest and in transit. Many award-winning firms are now moving toward a Zero Trust Security framework. This approach ensures that every access request is fully authenticated and authorised, regardless of where it originates.
Supply Chain Security and Incident Handling
You’re only as strong as your weakest link. You must assess the security levels of your third-party suppliers to ensure they don’t become a back door into your network. Alongside this, you need a robust plan for when things go wrong. This includes clear procedures for detecting and reporting threats. The nis2 compliance framework is strict about timelines. You’ll have just 24 hours to provide an “early warning” of a significant incident and a full 72 hours to submit a formal notification to the authorities.
Business Continuity and Cyber Hygiene
Resilience is about how quickly you can bounce back. Secure your communications with multi-factor authentication (MFA) and encrypted voice or video channels. Your backup management and disaster recovery planning must be tested regularly to ensure they actually work when needed. Don’t forget the human element. Basic cyber hygiene training for all staff members reduces the risk of successful phishing attacks. We’ve seen that 82% of breaches involve a human element, so educating your team is one of the most proactive steps you can take. It’s about building a culture of security that supports your long-term growth.
Implementing a Robust Cyber Risk Management Strategy
Moving from a static checklist to active implementation marks the start of your real journey toward nis2 compliance. You can’t treat this as a simple IT project. It requires a structured plan that reshapes how your business handles data and risk. A “security-first” culture must start in the boardroom; it’s no longer just a task for the server room. When leadership prioritises cyber hygiene, the rest of the organisation follows suit. This shift ensures that every employee understands their role in protecting the company’s digital assets.
Relying on a one-off audit is a dangerous mistake. NIS2 requires continuous monitoring and proactive threat detection. Cyber threats don’t wait for your annual review. Our award-winning Managed IT Services deliver the constant oversight needed to identify and neutralise risks in real-time. We act as your dedicated partner, ensuring your systems remain resilient against the latest vulnerabilities. This proactive approach provides the peace of mind you need to focus on your core business goals.
The Role of Board Accountability
Directors and senior leaders now face unprecedented pressure. Under NIS2, management can be held personally liable for cybersecurity failures within their organisation. This isn’t just about corporate fines; it’s about individual accountability. You must implement mandatory cybersecurity training for all senior management to bridge the knowledge gap. Boards are now legally required to approve risk management measures and oversee their implementation directly. It’s about taking ownership of your digital safety at the highest level.
Gap Analysis: Finding Your Weak Points
Your first step is a thorough internal audit against the 10 pillars of NIS2. You need to identify where your current defences fall short. Start by prioritising “low-hanging fruit” like Multi-Factor Authentication (MFA) and rigorous patch management. UK government figures from 2024 show that 50% of all businesses experienced some form of cyber breach in the last 12 months. Using external experts provides an unbiased view of your infrastructure. We help you see the blind spots that internal teams might miss, ensuring your nis2 compliance strategy is watertight and robust.
Ready to secure your business and meet the 2026 standards? Book a chat with our North East experts today to start your gap analysis.
Partnering for Peace of Mind: Managed IT and NIS2 Compliance
Achieving nis2 compliance isn’t a one-off task. It’s a fundamental change in how your business operates and protects its digital assets. For most UK SMEs, the technical and administrative burden of these new regulations is simply too heavy to carry alone. Managing risk across complex supply chains while maintaining constant system availability requires resources that internal IT teams often lack. The complexity of the 2024 directive, which sees full enforcement by 2026, means that guesswork is no longer an option.
We are Cornerstone Business Solutions. As an award-winning technology partner based in the North East, we specialise in turning these regulatory hurdles into competitive advantages. Our team doesn’t just fix problems; we build resilient systems that protect your reputation and your bottom line. We bring professional authority and regional warmth to every project, ensuring you feel supported at every turn. We believe that technology should empower your growth, not hinder it with red tape.
How Cornerstone Simplifies Compliance
We take the guesswork out of security. Our managed security updates and patch management programmes ensure that vulnerabilities are closed before attackers can exploit them. We implement Cloud Solutions with built-in compliance features, allowing your team to work flexibly without compromising data integrity. This proactive approach reduces the risk of costly downtime and ensures your infrastructure meets the high standards required by modern legislation.
NIS2 requires strict incident reporting, often within 24 hours of a significant threat detection. Our proactive monitoring runs 24/7, identifying anomalies and mitigating risks in real-time. This level of oversight ensures you meet legal deadlines and keep your operations running smoothly. We provide the robust framework you need to demonstrate “appropriate and proportionate” security measures to regulators. You get the benefit of an enterprise-level security operations centre without the overheads of building one yourself.
Your Next Steps to a Secure Future
Securing your business shouldn’t feel like a battle. We start by booking a comprehensive cyber security audit with our expert team to identify exactly where your gaps are. From there, we develop a tailored roadmap that aligns with your specific business goals. This ensures every penny spent on IT delivers maximum value and directly contributes to your nis2 compliance status.
You deserve the peace of mind that comes from knowing your business is safe. Let’s have a chat about your current status and how we can help you achieve robust security without the stress. We’re here to be your long-term partner, providing the “can-do” attitude that North East businesses are famous for. Achieving compliance is a journey, and we’re ready to walk it with you.
Secure Your Competitive Edge for 2026 and Beyond
The 2026 regulatory shift represents a significant change for UK organisations. Acting now ensures you aren’t caught in a last-minute rush to meet strict security standards. Identifying your entity status and addressing the 10 pillars of nis2 compliance today creates a resilient foundation for your business growth. It’s about protecting your supply chain and maintaining the trust of your clients in an increasingly volatile digital landscape.
Cornerstone Business Solutions has spent over 15 years acting as a trusted partner for UK firms. Our multi-award-winning team works alongside global leaders like Microsoft, IBM, and Cisco to deliver world-class security with a friendly, regional touch. We’ll help you navigate these complex requirements with clear, proactive strategies that simplify your technology. Let’s work together to protect your reputation and provide the genuine peace of mind you deserve. You’ve built a great business; we’re here to help you keep it safe.
Book a Comprehensive NIS2 Gap Analysis with our Award-Winning Team
Frequently Asked Questions
Does NIS2 apply to UK businesses after Brexit?
Yes, NIS2 applies to UK businesses if they provide essential or important services within the EU or form part of an EU-based supply chain. Even though the UK has left the EU, your organisation must comply if you operate in sectors like energy, transport, or digital infrastructure and have a physical presence or customers in the Eurozone. Our award-winning team helps local firms navigate these cross-border rules to ensure your operations remain seamless and secure.
What is the deadline for NIS2 compliance in 2026?
The primary enforcement window for most UK supply chain partners intensifies in 2026, following the initial EU transposition deadline of 17 October 2024. While the core legislation is already active, many regional businesses are using 2026 as the critical milestone for completing full infrastructure audits. Starting your nis2 compliance journey now prevents a last-minute rush. We recommend a proactive approach to keep your North East business ahead of these evolving regulatory requirements.
What are the fines for failing to meet NIS2 requirements?
Fines for non-compliance are substantial, reaching up to £8.5 million or 2% of total global annual turnover for essential entities. For important entities, the ceiling is approximately £6 million or 1.4% of global turnover. These penalties demonstrate why robust cybersecurity is a foundation for business peace of mind. We implement tailored solutions that protect your bottom line from these heavy financial risks while building a more resilient digital environment.
What is the difference between an “Essential” and “Important” entity?
The main difference lies in the specific sector and the size of your organisation. Essential entities include large organisations in high-criticality sectors like energy, transport, and health with over 250 employees. Important entities typically cover medium-sized businesses in sectors such as postal services, waste management, and food production. Our experts help you identify your specific category to ensure your security measures are perfectly sized for your unique business needs.
How does NIS2 differ from the original NIS directive?
NIS2 significantly expands the scope of the original 2018 directive by including more sectors and introducing much stricter enforcement rules. It places personal liability on senior management for security failures and mandates more rigorous risk management across the entire supply chain. This update ensures that nis2 compliance covers a broader range of modern digital threats. We provide the expert analysis needed to transition your legacy systems to these tougher, modern standards.
Can my Managed IT provider help with NIS2 reporting?
Yes, your managed IT provider plays a vital role in meeting your reporting obligations through constant, proactive network monitoring. Our award-winning support team tracks threats in real-time, providing the precise data needed for the 24-hour early warning and 72-hour incident reports. We act as your long-term partner, handling the technical heavy lifting so you can focus on growing your North East business with total confidence and clarity.
Is Cyber Essentials enough to meet NIS2 standards?
Cyber Essentials is a brilliant starting point, but it doesn’t cover the full scope of NIS2 requirements on its own. While Cyber Essentials focuses on basic technical controls, NIS2 demands comprehensive risk management, supply chain security, and specific incident reporting timelines. Think of Cyber Essentials as the foundation and NIS2 as the complete, robust structure. We’ll help you build upon your existing certifications to reach full, award-winning compliance levels.
What are the incident reporting timelines under NIS2?
You must submit an initial “early warning” to relevant authorities within 24 hours of becoming aware of a significant incident. This is followed by a formal incident notification within 72 hours and a detailed final report within one month of the event. These tight deadlines require a highly organised response plan. Our local team ensures your systems are set up to detect and flag issues immediately, keeping your business on the right side of the law.
Tags: Cyber Security, EU Legislation, IT Compliance, NIS2, NIS2 Checklist, NIS2 Directive, Risk Management, UK business